Windows Command-Line Obfuscation
Por um escritor misterioso
Last updated 26 novembro 2024
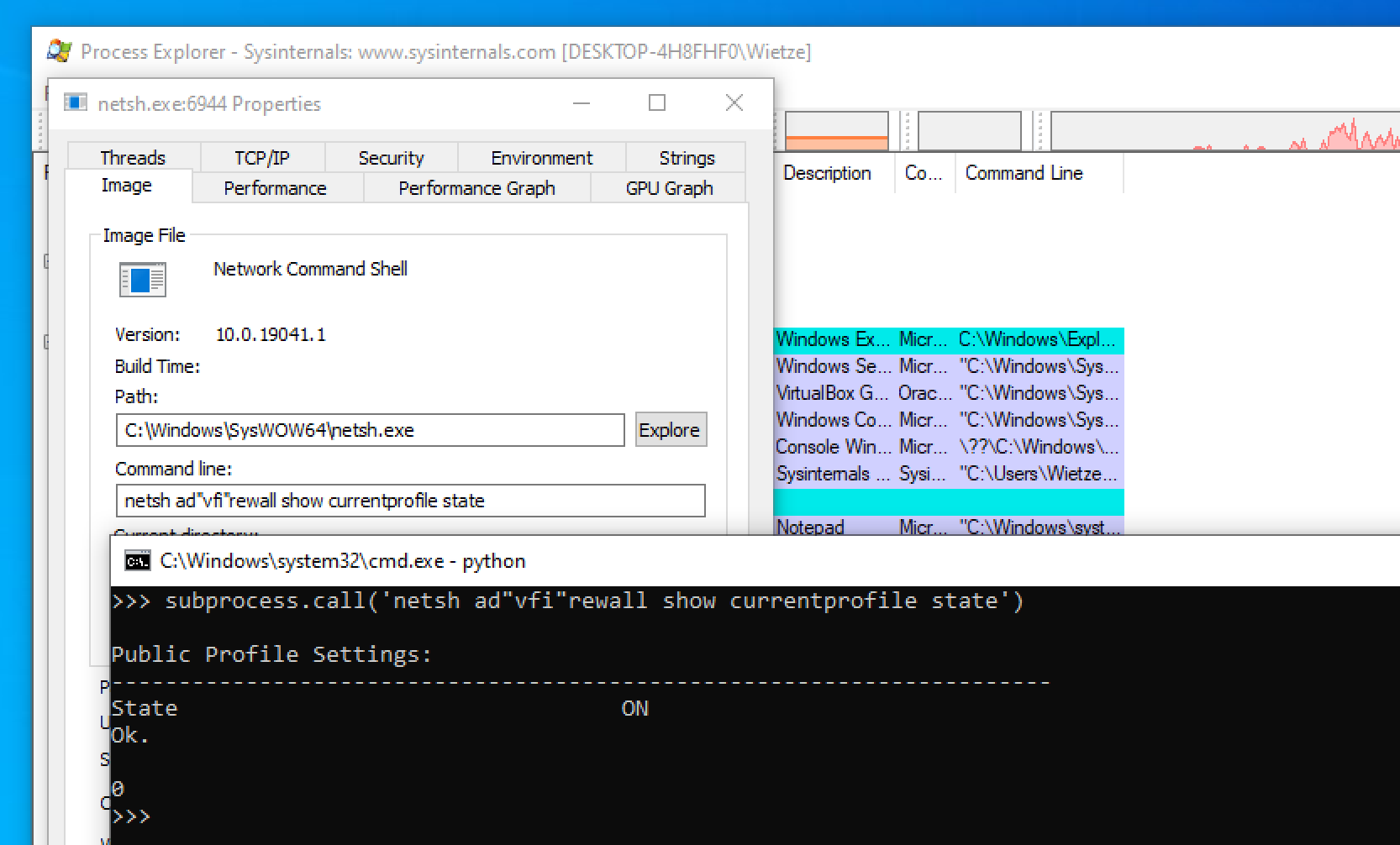
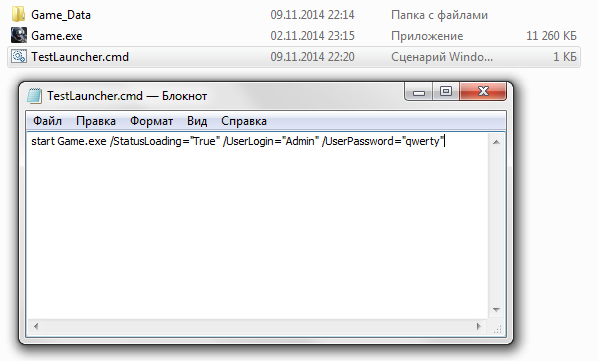
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.

hacking-material-books/obfuscation/simple_obfuscation.md at master

Using Deep Learning to Better Detect Command Obfuscation

Simple Obfuscation with PowerShell using Base64 Encoding
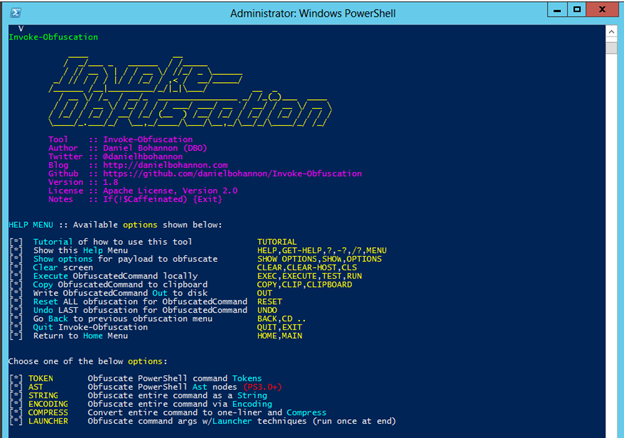
Invoke-Obfuscation — Hiding Payloads To Avoid Detection

Commandline Obfusaction - Red Team Notes

De-obfuscate/Decode Files or Information - Red Team Notes 2.0

Windows - Batch Obfuscated Stager

Tried and True Hacker Technique: DOS Obfuscation

Commandline Obfusaction - Red Team Notes
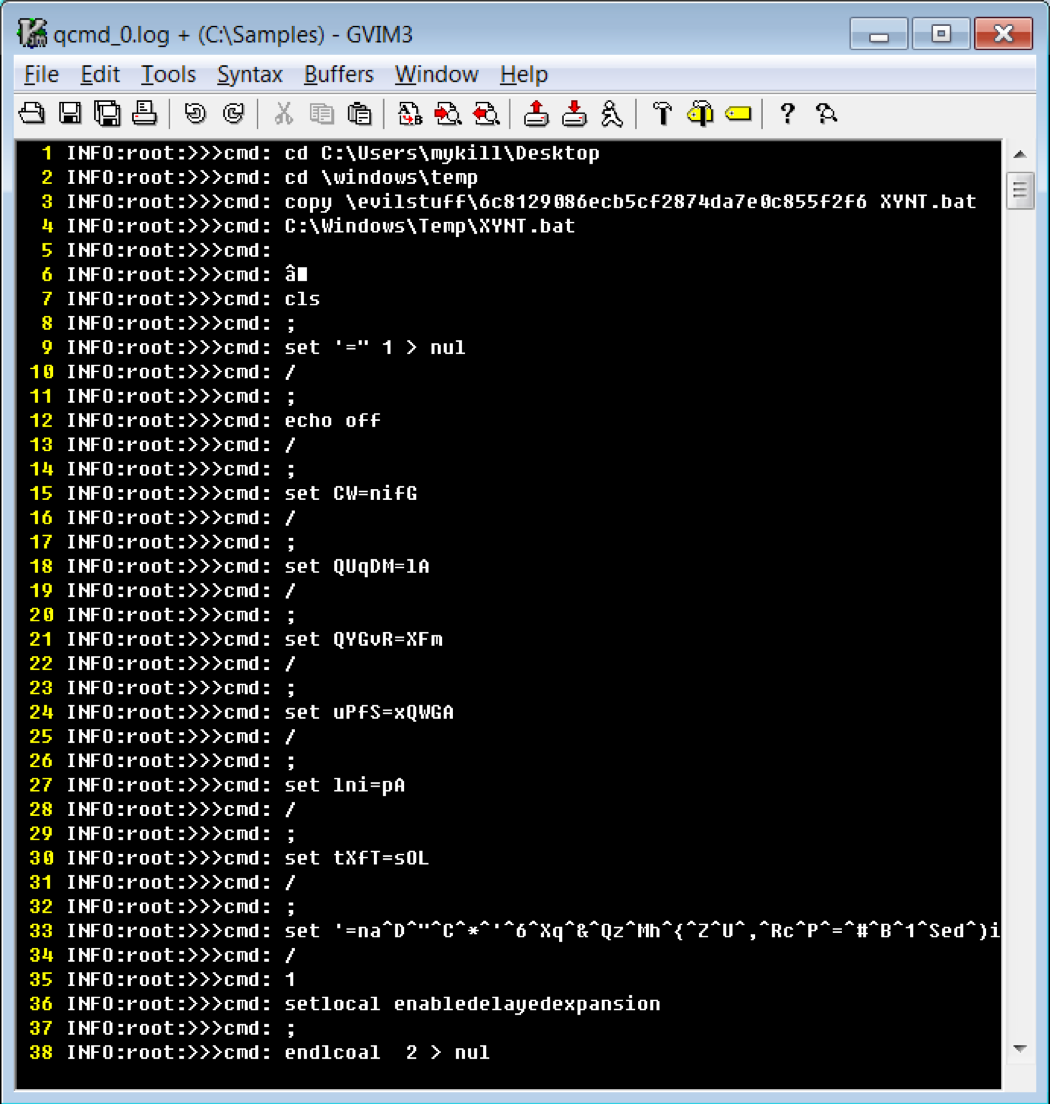
Cmd and Conquer: De-DOSfuscation with flare-qdb - REAL security
Recomendado para você
-
 Use PowerShell to execute an exe – 4sysops26 novembro 2024
Use PowerShell to execute an exe – 4sysops26 novembro 2024 -
 cmd - How do i run a program with arguments and as administrator26 novembro 2024
cmd - How do i run a program with arguments and as administrator26 novembro 2024 -
 cmd - Running .exe files with user arguments in python - Stack26 novembro 2024
cmd - Running .exe files with user arguments in python - Stack26 novembro 2024 -
 Command line arguments to PC Project.EXE ? - Unity Forum26 novembro 2024
Command line arguments to PC Project.EXE ? - Unity Forum26 novembro 2024 -
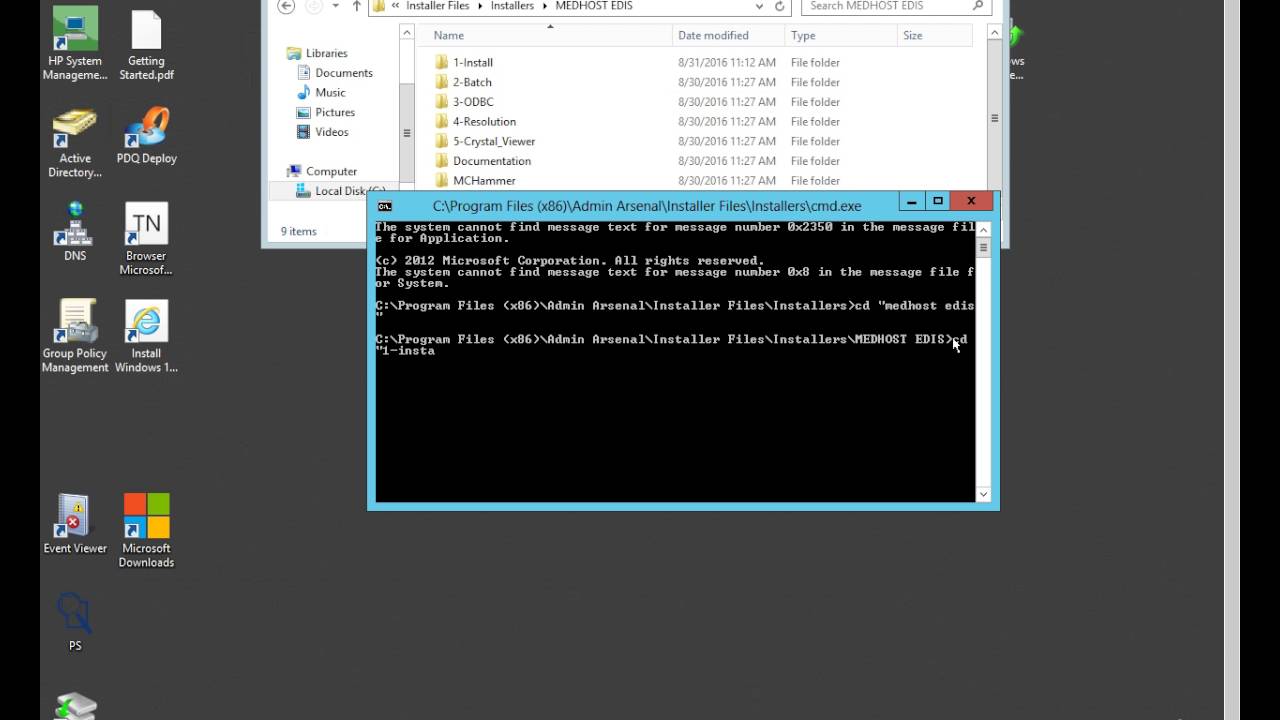
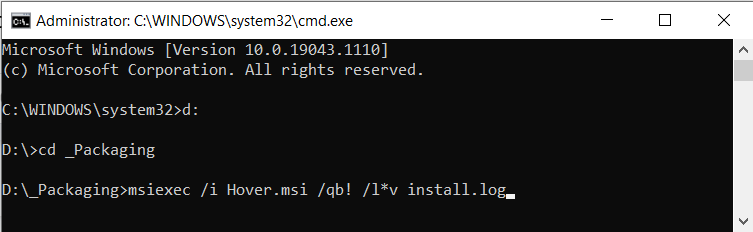 Silently Install EXE and MSI setup applications (Unattended) - How26 novembro 2024
Silently Install EXE and MSI setup applications (Unattended) - How26 novembro 2024 -
 How to Get Silent Install parameters from a .exe26 novembro 2024
How to Get Silent Install parameters from a .exe26 novembro 2024 -
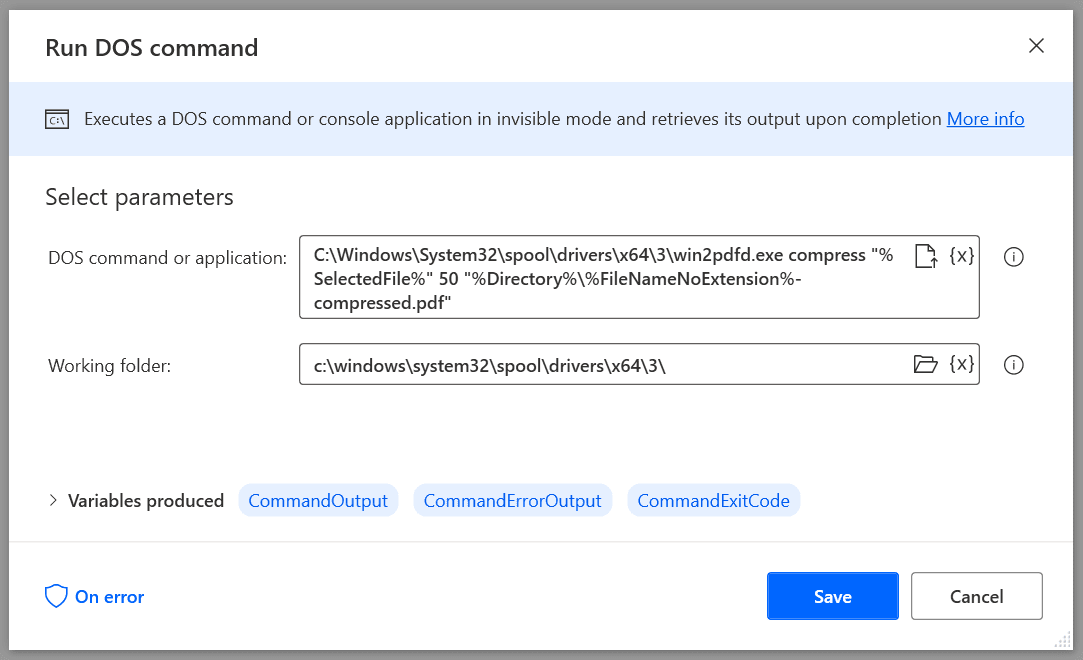 How To Use The Win2PDF Command Line With Power Automate Desktop26 novembro 2024
How To Use The Win2PDF Command Line With Power Automate Desktop26 novembro 2024 -
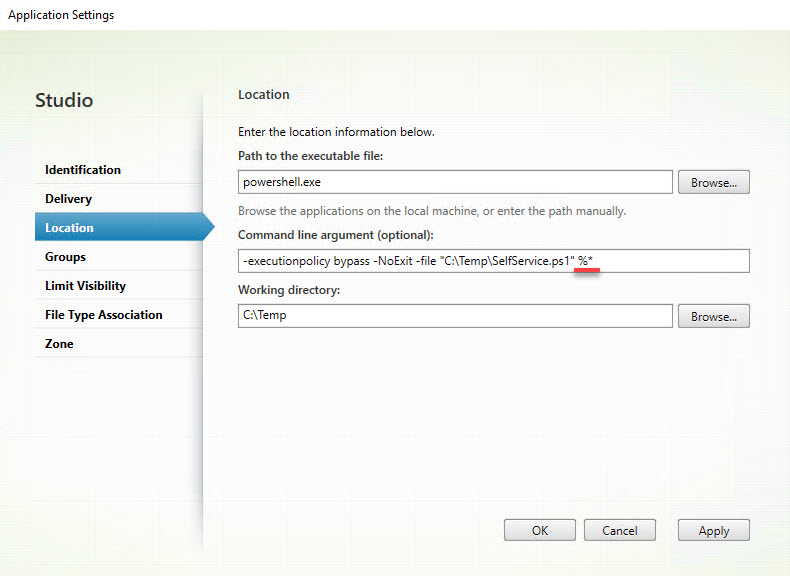 Parsing multiple parameters using the Citrix SelfService.exe26 novembro 2024
Parsing multiple parameters using the Citrix SelfService.exe26 novembro 2024 -
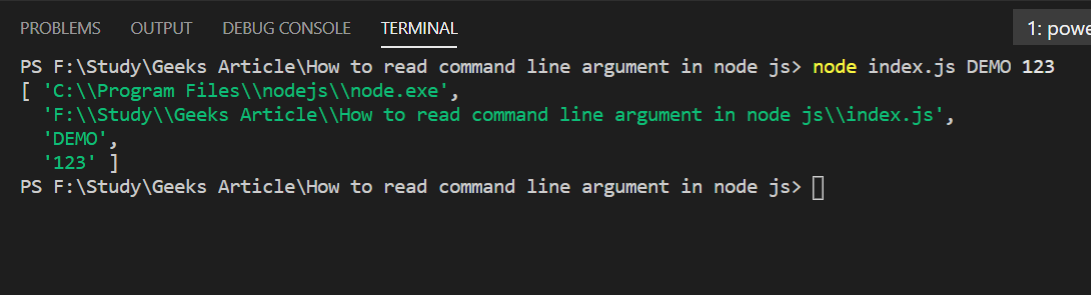 How to read command line arguments in Node.js ? - GeeksforGeeks26 novembro 2024
How to read command line arguments in Node.js ? - GeeksforGeeks26 novembro 2024 -
 executable - How can I find out if an .EXE has Command-Line26 novembro 2024
executable - How can I find out if an .EXE has Command-Line26 novembro 2024
você pode gostar
-
 THE TRUE ROBLOX STORY OF GUEST 666!26 novembro 2024
THE TRUE ROBLOX STORY OF GUEST 666!26 novembro 2024 -
 Onde assistir o filme do mario 2023 dublado|Pesquisa do TikTok26 novembro 2024
Onde assistir o filme do mario 2023 dublado|Pesquisa do TikTok26 novembro 2024 -
 Jogos Mortais O final - Zinema26 novembro 2024
Jogos Mortais O final - Zinema26 novembro 2024 -
 Monaliz Meu Controle 30cpr - Sanibras - FarmaViver26 novembro 2024
Monaliz Meu Controle 30cpr - Sanibras - FarmaViver26 novembro 2024 -
Chat with Pou Emo, Total: 0 chats, 0 messages26 novembro 2024
-
Canais e Grupos Telegram - ▶️TIPO #GRUPO 📌CATEGORIAS: #Humor #Memes #Chat 🆔NOME: Grupo The Merda 💩👍 Vamos interagir com os doidos no grupo 😂😂 😃👉26 novembro 2024
-
 SMS Legal PRO: Não reclame da vida, levante a cabeça. Dias ruins26 novembro 2024
SMS Legal PRO: Não reclame da vida, levante a cabeça. Dias ruins26 novembro 2024 -
 Hospital Visão26 novembro 2024
Hospital Visão26 novembro 2024 -
 Jogos PG em 2023 Álbum de fotos faça você mesmo, Dia dos pais26 novembro 2024
Jogos PG em 2023 Álbum de fotos faça você mesmo, Dia dos pais26 novembro 2024 -
format(webp)) Oshi no Ko Anime lässt Aprilscherz zur Realität werden - Crunchyroll News26 novembro 2024
Oshi no Ko Anime lässt Aprilscherz zur Realität werden - Crunchyroll News26 novembro 2024

