Malware analysis Malicious activity
Por um escritor misterioso
Last updated 26 março 2025

Feature Extraction and Detection of Malwares Using Machine Learning

TryHackMe Hacktivities
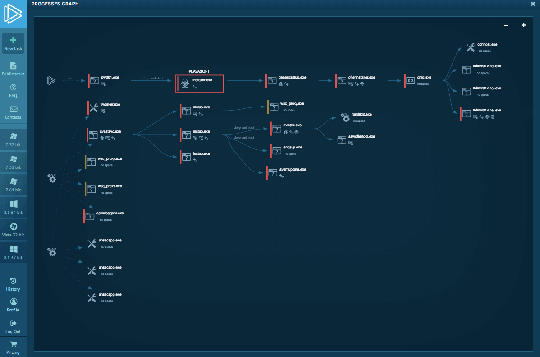
Interactive Online Malware Sandbox

MetaDefender Cloud Advanced threat prevention and detection

Malware Analysis: Steps & Examples - CrowdStrike

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

Malware analysis metasploit.bat Malicious activity

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Interactive Online Malware Sandbox

Malware analysis AIO_4.9.8__ed.rar Malicious activity

Brute Force Attacks: Password Protection
TryHackMe Hacktivities

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

Malware analysis index.html Malicious activity
Recomendado para você
-
blox-fruits-hack · GitHub Topics · GitHub26 março 2025
-
 Get FREE ROBUX INSTANTLY for ROBLOX PLATFORM!26 março 2025
Get FREE ROBUX INSTANTLY for ROBLOX PLATFORM!26 março 2025 -
Get Robux Calc Daily Tool - Apps on Google Play26 março 2025
-
 best apk mods roblox mobile|TikTok Search26 março 2025
best apk mods roblox mobile|TikTok Search26 março 2025 -
 Free Robux Generator Roblox Free Robux Codes Weekender Tote Bag by26 março 2025
Free Robux Generator Roblox Free Robux Codes Weekender Tote Bag by26 março 2025 -
 Robot Builder::Appstore for Android26 março 2025
Robot Builder::Appstore for Android26 março 2025 -
Telugu Gadgets26 março 2025
-
 Free Robux APK برای دانلود اندروید26 março 2025
Free Robux APK برای دانلود اندروید26 março 2025 -
 Malware analysis Malicious activity26 março 2025
Malware analysis Malicious activity26 março 2025 -
Free Robux Generator 2024: How to Collect 99999 Robux ✮✧✮ No Verification26 março 2025
você pode gostar
-
 WERE definição e significado26 março 2025
WERE definição e significado26 março 2025 -
 Haikyuu!! Facts That Prove Just How Much The Series Has Changed The Anime Game26 março 2025
Haikyuu!! Facts That Prove Just How Much The Series Has Changed The Anime Game26 março 2025 -
 chaturanga dandasana Archives - Yogateria26 março 2025
chaturanga dandasana Archives - Yogateria26 março 2025 -
 VEVOR Racing Simulator Steering Wheel Stand for G27 G29 PS4 G92026 março 2025
VEVOR Racing Simulator Steering Wheel Stand for G27 G29 PS4 G92026 março 2025 -
 L'Oréal Professionnel Dia Richesse Semi Permanent Hair Colour26 março 2025
L'Oréal Professionnel Dia Richesse Semi Permanent Hair Colour26 março 2025 -
 Red 2 Movie Poster (#20 of 21) - IMP Awards26 março 2025
Red 2 Movie Poster (#20 of 21) - IMP Awards26 março 2025 -
 50+ Aesthetic black hair codes + How to use26 março 2025
50+ Aesthetic black hair codes + How to use26 março 2025 -
 Granblue Fantasy Massive Revision/Upgrade26 março 2025
Granblue Fantasy Massive Revision/Upgrade26 março 2025 -
 yuzu encryption keys|TikTok Search26 março 2025
yuzu encryption keys|TikTok Search26 março 2025 -
 Call of The Night S2: Release Date, and Where to Watch26 março 2025
Call of The Night S2: Release Date, and Where to Watch26 março 2025