Malware analysis Malicious activity
Por um escritor misterioso
Last updated 19 janeiro 2025

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Info stealers and how to protect against them

Comprehensive Protection Strategies Against Cyber Threats

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware analysis metasploit.bat Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis Benefits Incident Response

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

An Elastic approach to large-scale dynamic malware analysis — Elastic Security Labs

Dynamic malware analysis [34]

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Endpoint Detection and Response, Free - What is EDR Security?
Recomendado para você
-
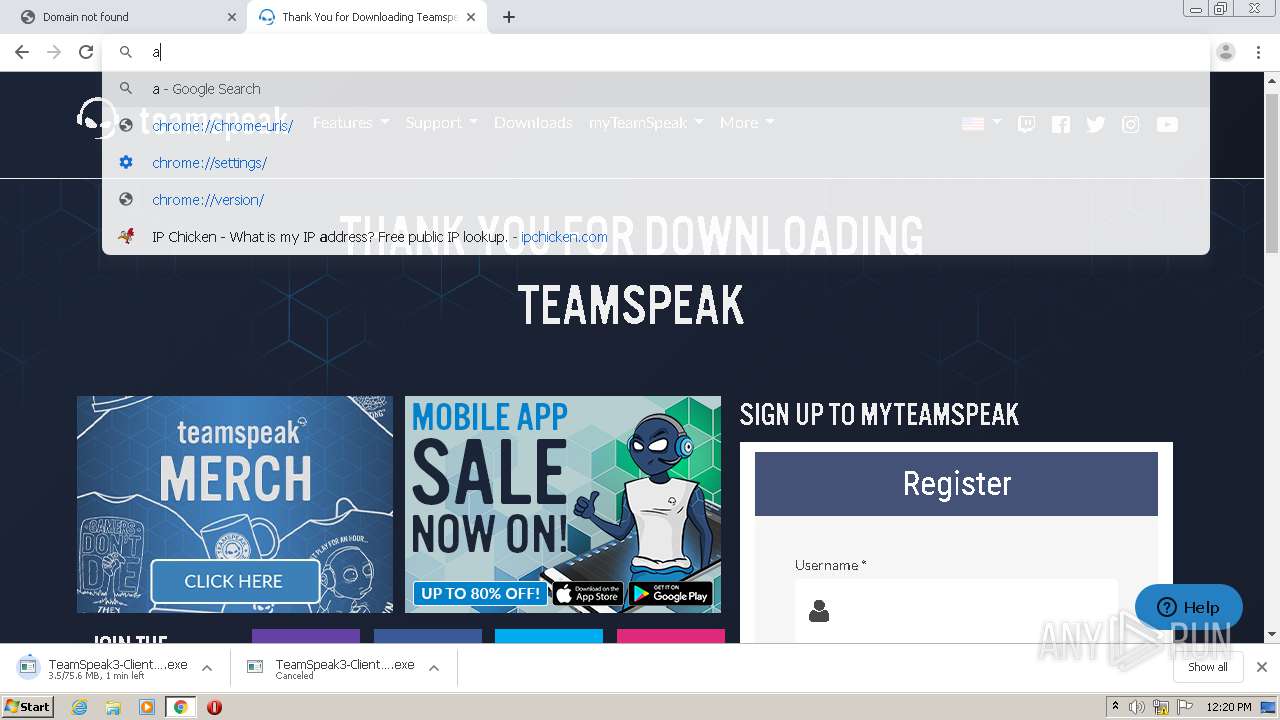
 IPChicken, Woo hoo! Lightspeed!, Richard De Guzman19 janeiro 2025
IPChicken, Woo hoo! Lightspeed!, Richard De Guzman19 janeiro 2025 -
 Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders19 janeiro 2025
Setup OrthoInTouch with topsOrtho - OrthoInTouch - Appointment Reminders19 janeiro 2025 -
 IPchicken at the terminal19 janeiro 2025
IPchicken at the terminal19 janeiro 2025 -
![🔴LIVE] How to know my Local PC IP address?](https://i.ytimg.com/vi/HbDJUHhXKhg/maxresdefault.jpg) 🔴LIVE] How to know my Local PC IP address?19 janeiro 2025
🔴LIVE] How to know my Local PC IP address?19 janeiro 2025 -
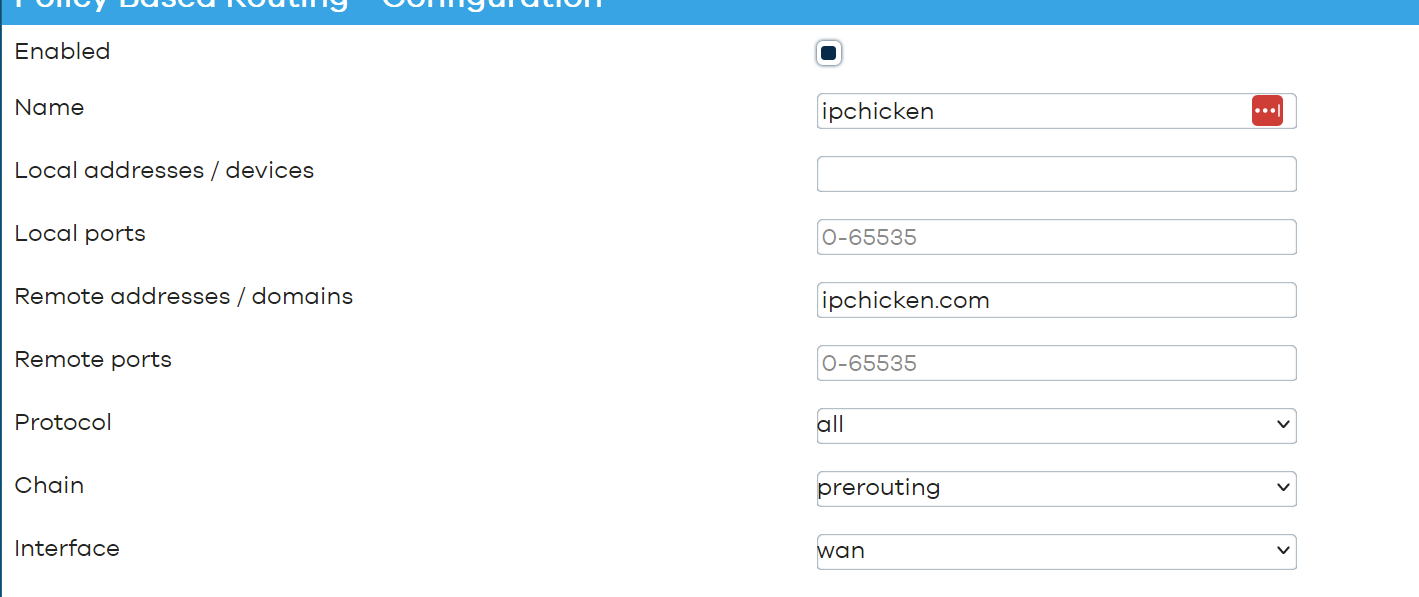 PBR with MulladVPN - Network and Wireless Configuration - OpenWrt Forum19 janeiro 2025
PBR with MulladVPN - Network and Wireless Configuration - OpenWrt Forum19 janeiro 2025 -
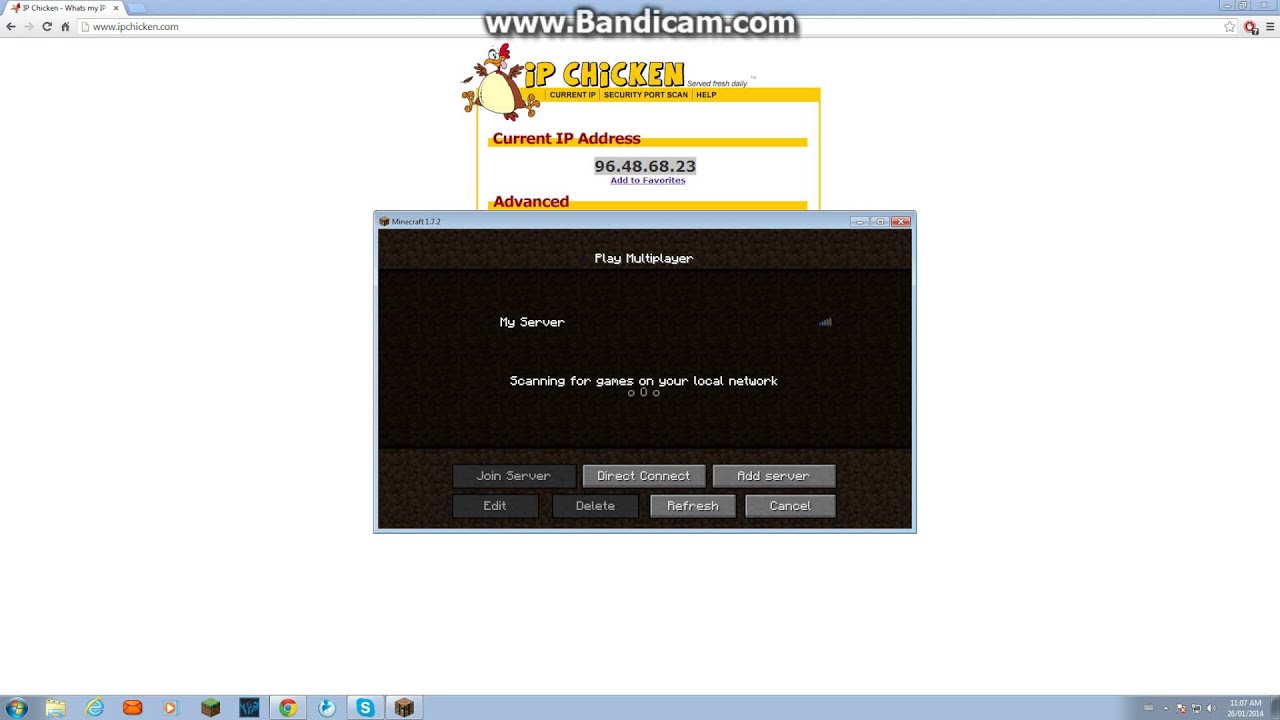 How to use ipchicken to access your minecraft server19 janeiro 2025
How to use ipchicken to access your minecraft server19 janeiro 2025 -
 like ip chicken 🐔🐔🐔 Ip chicken, Smart city, Coding19 janeiro 2025
like ip chicken 🐔🐔🐔 Ip chicken, Smart city, Coding19 janeiro 2025 -
 American Shoemaking Machinery at the Frankfort Leather Fair. Acorn-Storing Birds. W (IP Chicken Hatching by Electricity. Salmon from the Arctic Regions., scientific american, 1881-11-26 Stock Photo - Alamy19 janeiro 2025
American Shoemaking Machinery at the Frankfort Leather Fair. Acorn-Storing Birds. W (IP Chicken Hatching by Electricity. Salmon from the Arctic Regions., scientific american, 1881-11-26 Stock Photo - Alamy19 janeiro 2025 -
 Instant Pot Olive Garden Chicken Pasta - Sparkles to Sprinkles19 janeiro 2025
Instant Pot Olive Garden Chicken Pasta - Sparkles to Sprinkles19 janeiro 2025 -
 Google now let you find your IP address via search query - Sorry whatismyip.com - Pureinfotech19 janeiro 2025
Google now let you find your IP address via search query - Sorry whatismyip.com - Pureinfotech19 janeiro 2025
você pode gostar
-
 Valvrave The Liberator - English Dub TRAILER - MLXR Dubs19 janeiro 2025
Valvrave The Liberator - English Dub TRAILER - MLXR Dubs19 janeiro 2025 -
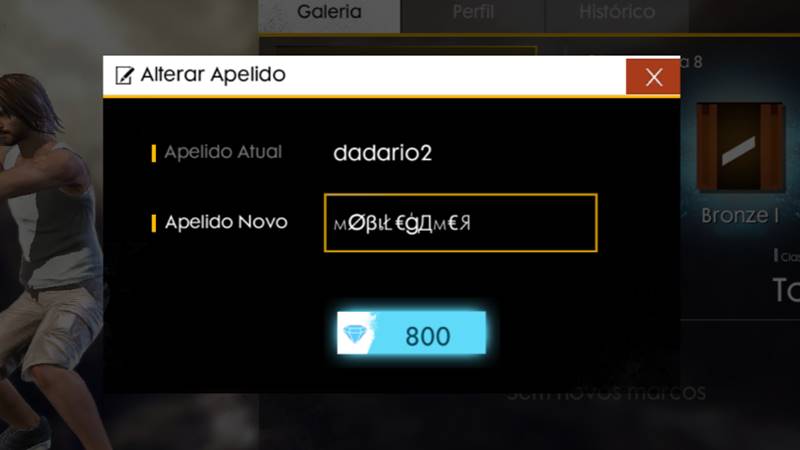 Nomes Free Fire - Gerador de Nick e Nomes para Free Fire - FREEFIRENEWS19 janeiro 2025
Nomes Free Fire - Gerador de Nick e Nomes para Free Fire - FREEFIRENEWS19 janeiro 2025 -
 Clockwork Planet19 janeiro 2025
Clockwork Planet19 janeiro 2025 -
Bicicleta : Jogos de BMX – Apps no Google Play19 janeiro 2025
-
Moto Raging Corrida Infantil - Bs Toys19 janeiro 2025
-
 03-SET-2017 - COPA JUVENTUS FUTEBOL FEMININO - JUVENTUS 2 …19 janeiro 2025
03-SET-2017 - COPA JUVENTUS FUTEBOL FEMININO - JUVENTUS 2 …19 janeiro 2025 -
 Quantos gols Gabigol marcou na carreira?19 janeiro 2025
Quantos gols Gabigol marcou na carreira?19 janeiro 2025 -
 Go-toubun no hanayome Anime girl drawings, Kawaii anime, Anime19 janeiro 2025
Go-toubun no hanayome Anime girl drawings, Kawaii anime, Anime19 janeiro 2025 -
 Hunter X Hunter Season 7 waits: 2021 return of Megumi Han's Gon, Mariya Ise's Killua is for an escape room game19 janeiro 2025
Hunter X Hunter Season 7 waits: 2021 return of Megumi Han's Gon, Mariya Ise's Killua is for an escape room game19 janeiro 2025 -
 Testingcheatsenabled, The Sims Wiki19 janeiro 2025
Testingcheatsenabled, The Sims Wiki19 janeiro 2025
