Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Last updated 26 março 2025

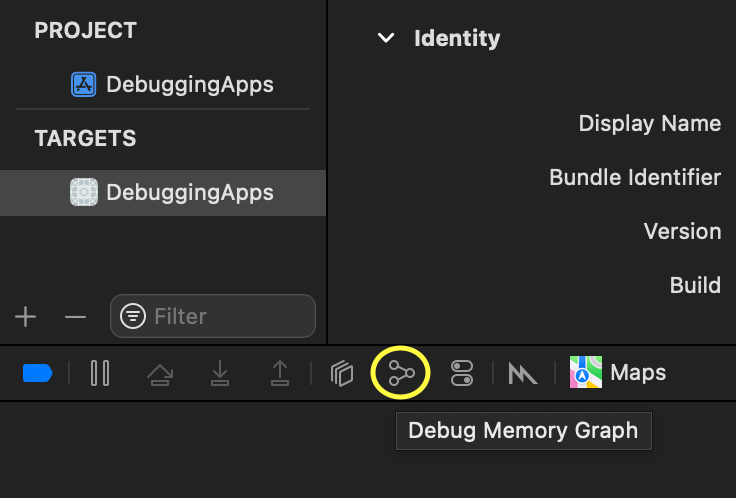
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.
Future Internet, Free Full-Text
Hacking the Xbox
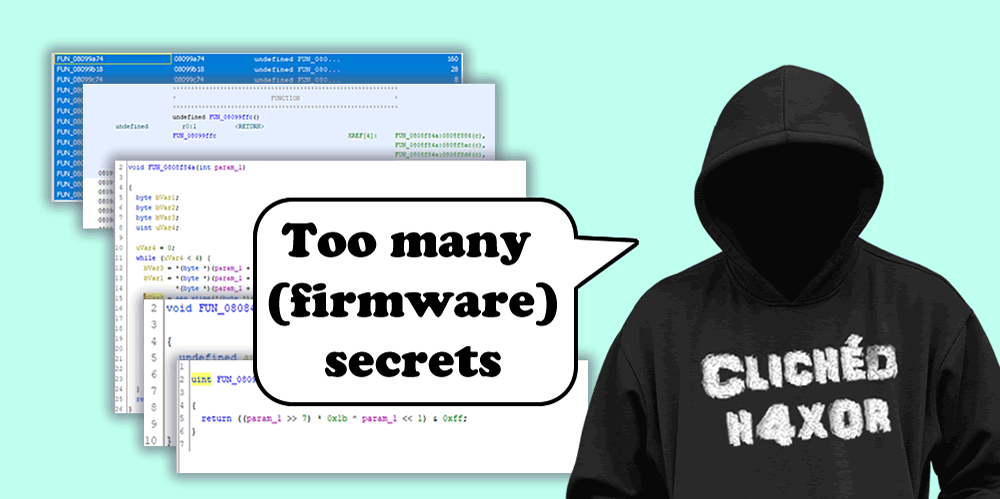
Reverse Engineering Keys from Firmware. A how-to
How to Reverse Engineer an iOS App, by Zafar Ivaev

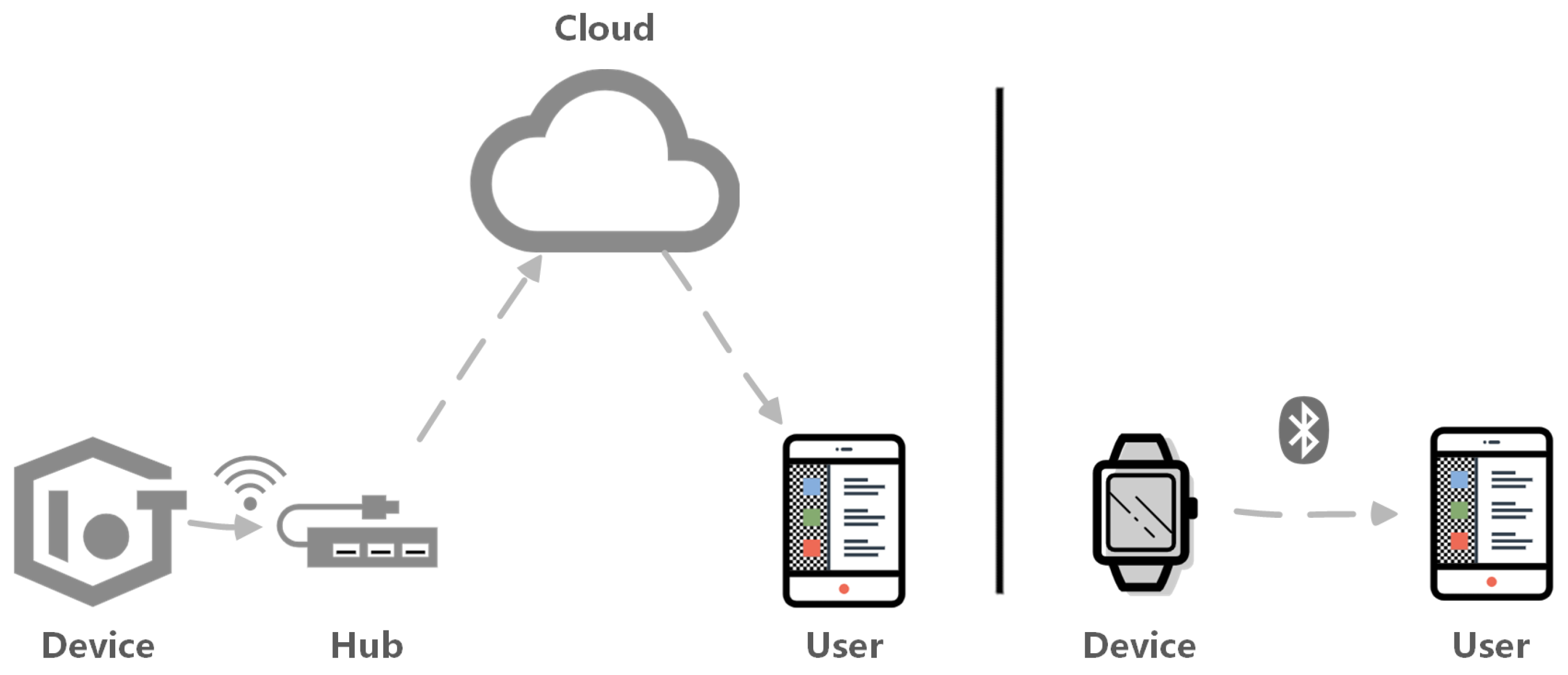
Reverse Engineering of a Not-so-Secure IoT Device
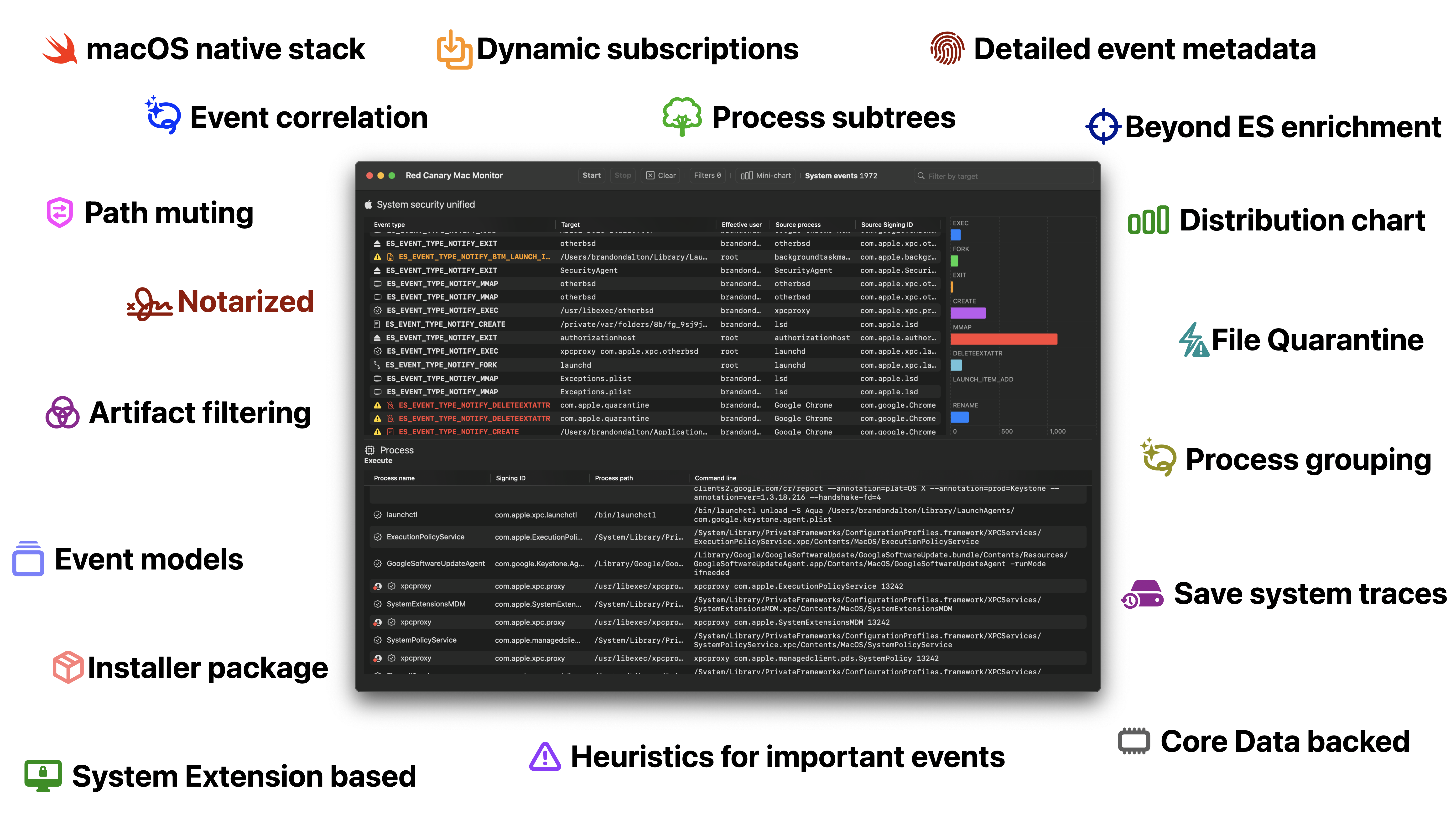
Red Canary Mac Monitor - An Advanced, Stand-Alone System Monitoring Tool Tailor-Made For macOS Security Research
Used Book in Good Condition Highlight, take notes, and search in the book

Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation

Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend

Tampering and Reverse Engineering on iOS - OWASP MASTG
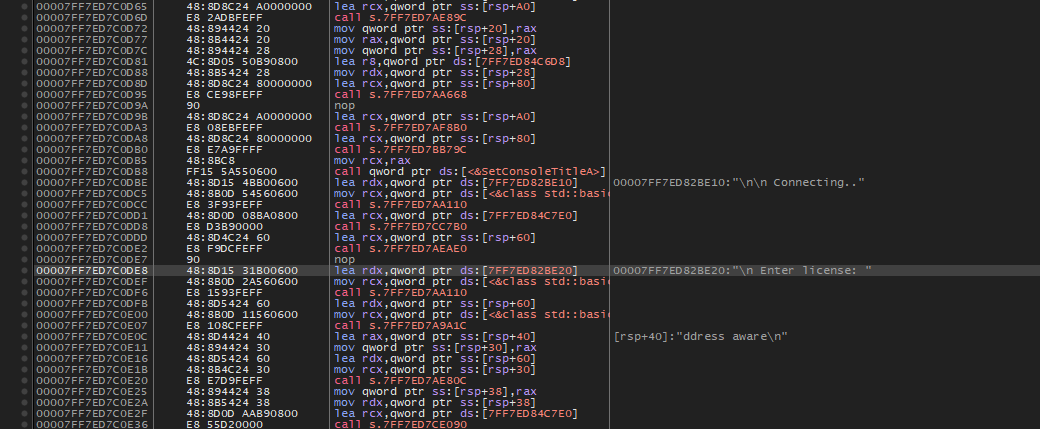
Reverse Engineering: Binary Security, by Totally_Not_A_Haxxer

Mastering Malware Analysis

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started
Recomendado para você
-
roblox-api · GitHub Topics · GitHub26 março 2025
-
BuxBack - Earn R$26 março 2025
-
rbxgum.com Traffic Analytics, Ranking Stats & Tech Stack26 março 2025
-
 5731) VÍDEOS DE COMO H4CK34R CONT4S NO R0BL0X26 março 2025
5731) VÍDEOS DE COMO H4CK34R CONT4S NO R0BL0X26 março 2025 -
como ver los codigos de rbx gum en discord|Búsqueda de TikTok26 março 2025
-
Cheeks Joy Blush Face Roblox Item - Rolimon's26 março 2025
-
robloxapi · GitHub Topics · GitHub26 março 2025
-
 Helix Studios, Hiring Advanced Scripter, 20K RBX - Recruitment - Developer Forum26 março 2025
Helix Studios, Hiring Advanced Scripter, 20K RBX - Recruitment - Developer Forum26 março 2025 -
 What are some legit websites that give free Robux in August 2022? - Quora26 março 2025
What are some legit websites that give free Robux in August 2022? - Quora26 março 2025 -
 Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend26 março 2025
Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend26 março 2025
você pode gostar
-
 Fabricante de guarnições de borracha - Autotravi26 março 2025
Fabricante de guarnições de borracha - Autotravi26 março 2025 -
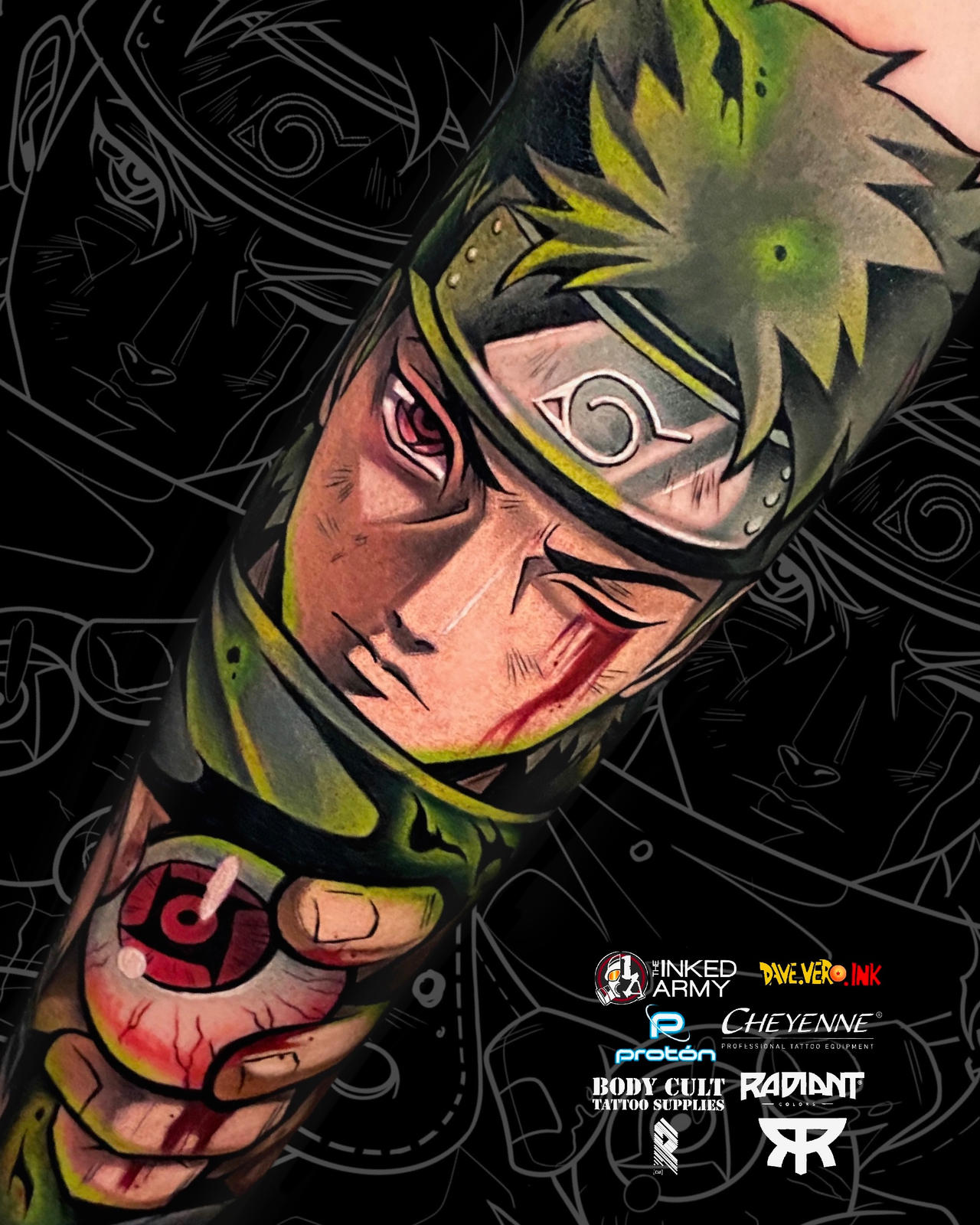 Shisui Uchiha Tattoo by DaveVeroInk by DaveVeroInk on DeviantArt26 março 2025
Shisui Uchiha Tattoo by DaveVeroInk by DaveVeroInk on DeviantArt26 março 2025 -
 FRAME lack Artworks & High Speed Drawing Techniques Book Anime Game Otaku Japan26 março 2025
FRAME lack Artworks & High Speed Drawing Techniques Book Anime Game Otaku Japan26 março 2025 -
 The Ruined Pizzaplex (FNaF Security Breach Ruin) - Chapter 1 - Wattpad26 março 2025
The Ruined Pizzaplex (FNaF Security Breach Ruin) - Chapter 1 - Wattpad26 março 2025 -
 ROBLOX MM2 MULTIPLE ITEMS IN PACKS OF 10!!!!26 março 2025
ROBLOX MM2 MULTIPLE ITEMS IN PACKS OF 10!!!!26 março 2025 -
 Pokemon Go Plus review: is Nintendo's first smartphone accessory worth the price?26 março 2025
Pokemon Go Plus review: is Nintendo's first smartphone accessory worth the price?26 março 2025 -
 Roger Milla was so amazing a lie sat unchanged on Wiki for two months26 março 2025
Roger Milla was so amazing a lie sat unchanged on Wiki for two months26 março 2025 -
 Uncharted: Legacy of Thieves Collection PC Review – An Exquisite Set of Adventures26 março 2025
Uncharted: Legacy of Thieves Collection PC Review – An Exquisite Set of Adventures26 março 2025 -
 Kawaii Semi-Estéreo T-shirt de Coelho Roxo dos Desenhos Animados26 março 2025
Kawaii Semi-Estéreo T-shirt de Coelho Roxo dos Desenhos Animados26 março 2025 -
 The Barber Shop by Bee Tracks - Play Online - Game Jolt26 março 2025
The Barber Shop by Bee Tracks - Play Online - Game Jolt26 março 2025
